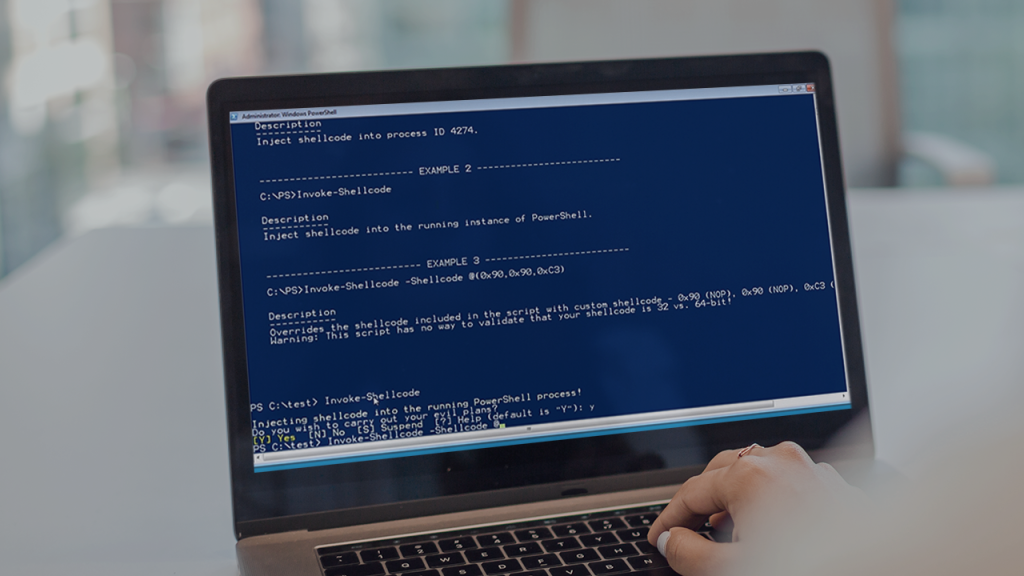
PowerSploit stands as a formidable collection of PowerShell modules designed specifically for offensive security tasks. It is not a single application but rather a comprehensive arsenal of scripts that security professionals, penetration testers, and red teamers leverage during security assessments. Its primary purpose is to aid in the post-exploitation phase of an attack, providing a powerful and versatile toolkit once initial system access has been established.
The framework’s immense power stems from its deep integration with PowerShell, a native Windows scripting and automation engine. Because PowerShell is pre-installed on virtually all modern Windows systems, PowerSploit can operate with a high degree of stealth, often bypassing traditional antivirus and security controls that are not configured to monitor PowerShell activity closely. This makes it an exceptionally effective tool for simulating real-world attack scenarios.
Understanding PowerSploit is crucial for both attackers and defenders. For ethical hackers, it provides the means to identify vulnerabilities, escalate privileges, and demonstrate the potential impact of a breach. For cybersecurity defenders, knowledge of PowerSploit’s capabilities is essential for threat hunting, incident response, and building robust defenses against the very techniques it employs.
Core Functionality and Purpose
A PowerShell-Based Arsenal
PowerSploit is fundamentally a library of PowerShell scripts rather than a standalone executable program. This modular design allows users to import only the specific functions they need for a given task. Its open-source nature means it is constantly being updated and vetted by the security community, ensuring it reflects current attack methodologies and techniques used by malicious actors in the wild.
Targeting Windows Environments
The framework is purpose-built for Windows ecosystems. It leverages the deep integration of PowerShell within the operating system to interact with core system components, the Active Directory domain structure, and other Windows-specific services. This native compatibility allows for powerful interactions that would be difficult to achieve with external tools, providing seamless control over a compromised Windows host.
The Post-Exploitation Focus
While some modules can assist with initial access, PowerSploit truly excels in the post-exploitation phase. After an attacker gains a foothold, this toolkit helps them escalate privileges, move laterally across the network, and maintain persistence. Its functions are designed to map out the internal network, gather sensitive credentials, and exfiltrate valuable data from the target environment.
Key Modules for Reconnaissance
Network Discovery
PowerSploit includes modules that can actively scan the network to discover other hosts, open ports, and shared network resources. These tools help an attacker build a detailed map of the target environment, identifying critical infrastructure like domain controllers, file servers, and database servers that may be high-value targets for further compromise or lateral movement.
User and Group Enumeration
Gathering information about domain users, groups, and permissions is a critical step. PowerSploit can query Active Directory to identify accounts with privileged access, such as domain or enterprise administrators. This information is vital for planning privilege escalation attacks, as compromising a high-privilege account can give an attacker complete control over the entire Windows domain.
Gathering System Information
Detailed system reconnaissance is key to identifying potential vulnerabilities. PowerSploit can pull extensive information from a compromised machine, including its configuration, installed software, and security settings. This data helps attackers find weak points to exploit for escalating their privileges or moving to other systems on the network.
- Operating system version and architecture
- Installed applications and missing patches
- Network configuration and active connections
- Running processes and associated service accounts
Privilege Escalation Techniques
Abusing Misconfigured Services
One common pathway to higher privileges is through improperly configured Windows services. PowerSploit can scan for services that a low-privilege user has permission to modify. If such a service runs with elevated privileges, an attacker can change its executable path to a malicious program, causing it to run with SYSTEM-level rights on the next reboot or service start.
Exploiting Vulnerable Drivers
The framework can also check for third-party drivers installed on the system that are known to be vulnerable or have weak security permissions. By exploiting a flawed driver, an attacker can execute code directly in the Windows kernel, achieving the highest possible level of privilege and completely bypassing many of the operating system’s built-in security controls.
DLL Hijacking Opportunities
DLL hijacking is a technique where an attacker tricks a legitimate application into loading a malicious dynamic-link library (DLL) instead of the one it expects. PowerSploit helps identify applications and processes that search for DLLs in insecure paths. By placing a crafted DLL in one of these locations, an attacker can have their code executed with the privileges of the targeted process.
Maintaining Access and Persistence
Creating Scheduled Tasks
A classic persistence method involves creating a new scheduled task that executes a malicious payload at a specified interval or when a user logs on. PowerSploit simplifies this process by using PowerShell to create, modify, and hide these tasks within the Windows Task Scheduler, ensuring the attacker’s code continues to run even after the system is rebooted.
Modifying Registry Keys
The Windows Registry is another common location for establishing persistence. PowerSploit provides functions to add entries to registry keys that are automatically checked by the operating system during startup. This ensures that a malicious script or executable is launched every time the system boots or a specific user logs in, providing a persistent backdoor.
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
- Image File Execution Options (IFEO) for process hijacking
- Service configuration registry keys for persistent services
WMI Event Subscription
For a more advanced and stealthy persistence mechanism, PowerSploit can leverage Windows Management Instrumentation (WMI). An attacker can create a permanent event subscription that triggers a PowerShell script in response to a specific system event, such as a user logging in or a new process being created. This method is often difficult to detect with traditional security tools.
Exfiltration and Data Theft
Compressing and Encrypting Data
Before stealing data, attackers often need to package it to avoid detection. PowerSploit includes modules that can compress multiple files into a single archive and even apply a layer of encryption. This makes the data smaller for faster transfer and helps it evade network-based security controls that might be inspecting file contents for known sensitive information patterns.
Covert Channels
Exfiltrating data without raising alarms requires using covert channels that blend in with legitimate network traffic. PowerSploit can help establish these channels, hiding the data transfer within protocols that are less likely to be heavily monitored. This allows an attacker to slowly siphon information out of the network over an extended period.
- DNS tunneling to hide data in DNS queries
- ICMP tunneling using ping packets
- Utilizing legitimate cloud services like Pastebin
- Custom TCP/UDP protocols to bypass firewalls
Script-Based File Transfer
Instead of using common file transfer protocols like FTP that might be blocked, PowerSploit can use PowerShell itself to download or upload files. It can make web requests to a remote server controlled by the attacker, allowing it to pull down additional tools or exfiltrate data using HTTP or HTTPS, which is almost always allowed out of a network.
The Ethical and Defensive Perspective
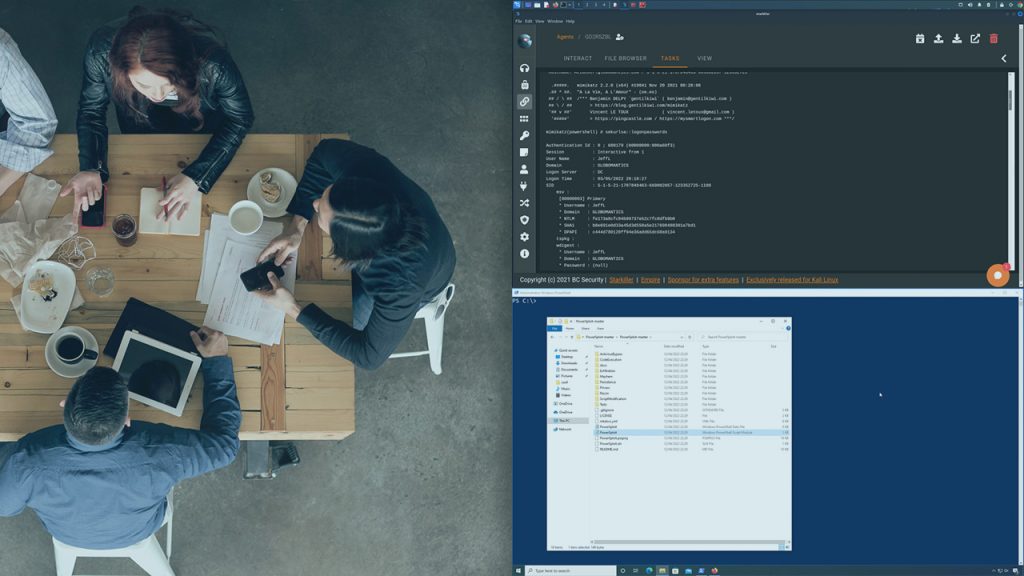
Red Team and Penetration Testing
In the hands of ethical hackers, PowerSploit is an invaluable tool for simulating real-world cyberattacks. Red teams use it to test an organization’s detection and response capabilities. By demonstrating how an attacker can move laterally, escalate privileges, and steal data, they provide concrete evidence of security gaps that need to be addressed by the organization.
Blue Team Threat Hunting
Conversely, cybersecurity defenders (the blue team) study PowerSploit to better understand their adversaries. By learning the techniques and command-line signatures associated with its use, they can create more effective detection rules. Threat hunters actively search for indicators of PowerSploit activity in logs and system events to identify ongoing or past intrusions that may have gone unnoticed.
Importance of PowerShell Logging
The best defense against PowerSploit is comprehensive visibility into PowerShell activity. Enabling features like Script Block Logging and Module Logging within Windows is critical. These advanced logging capabilities record the actual content of PowerShell scripts as they are executed, providing defenders with the detailed evidence needed to detect, analyze, and respond to attacks leveraging this powerful framework.
Conclusion
PowerSploit serves as a critical post-exploitation framework for Windows, offering an extensive suite of modules for reconnaissance, privilege escalation, persistence, and data exfiltration. Its dual nature makes it a potent weapon for malicious actors and an indispensable tool for security professionals testing defenses. Understanding its capabilities is paramount for building resilient security postures and effectively hunting for threats within modern enterprise environments.