PowerSploit stands as one of the most formidable post-exploitation frameworks in the cybersecurity landscape today. Developed as a collection of PowerShell modules, this tool has gained notoriety among both penetration testers and malicious actors for its extensive capabilities in maintaining persistence, escalating privileges, and exfiltrating data from compromised systems. The framework’s integration with PowerShell makes it particularly dangerous as it leverages a legitimate Windows administration tool, making detection challenging for traditional security solutions.
The detection of PowerSploit activities has become increasingly critical for organizations seeking to protect their digital assets. Since PowerSploit operates primarily in memory and can leave minimal forensic evidence, traditional antivirus solutions often fail to identify its presence. Attackers utilizing this framework can move laterally across networks, establish persistent backdoors, and remain undetected for extended periods, potentially causing significant damage to an organization’s infrastructure, data integrity, and reputation.
PowerSploit Framework
What is PowerSploit and Its Capabilities
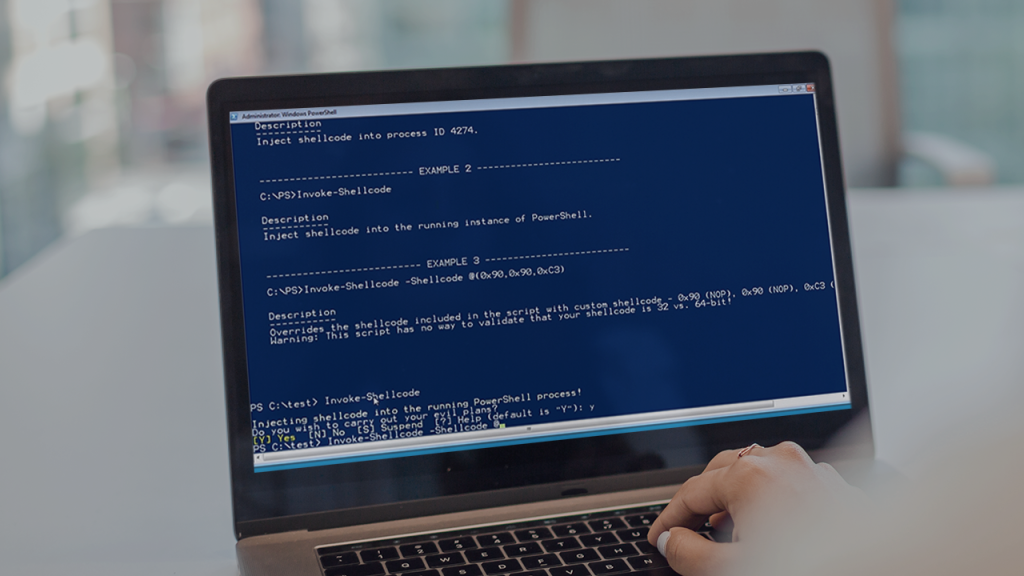
PowerSploit emerged as a sophisticated penetration testing framework designed specifically for PowerShell environments. Developed initially for legitimate security testing purposes, it has since been adopted by malicious actors due to its powerful capabilities and ease of use. The framework consists of numerous modules that can perform various post-exploitation tasks including code execution, credential harvesting, privilege escalation, and data exfiltration. What makes PowerSploit particularly dangerous is its ability to operate entirely in memory, leaving minimal traces on disk that traditional antivirus solutions might detect.
The framework’s modular architecture allows attackers to customize their approach based on the target environment and their objectives. PowerSploit can bypass application whitelisting, manipulate Windows security features, and establish persistence mechanisms that survive system reboots. Its capabilities extend to manipulating Windows tokens, creating backdoors, and even enabling attackers to move laterally across a network while remaining undetected. The framework’s integration with PowerShell means it can leverage trusted system processes to execute malicious activities, making it particularly challenging to distinguish between legitimate administrative tasks and malicious operations.
Common Attack Vectors Used by PowerSploit
Attackers typically deliver PowerSploit through various attack vectors that exploit system vulnerabilities or user trust. One common method involves phishing emails with malicious attachments or links that execute PowerShell commands when opened. Another approach utilizes web-based attacks where compromised websites deliver PowerSploit through drive-by downloads. Attackers may also leverage existing vulnerabilities in systems or applications to gain initial access before deploying PowerSploit for post-exploitation activities.
Once initial access is established, attackers often use PowerSploit to escalate privileges and move laterally across the network. The framework’s ability to bypass security controls makes it particularly effective in environments with weak security configurations. Attackers can exploit misconfigured permissions, unpatched systems, or weak credentials to expand their access. PowerSploit’s capabilities in credential harvesting enable attackers to obtain legitimate credentials, further facilitating their movement through the network while appearing as authorized users, which significantly complicates detection efforts.
Evolution of PowerSploit in Cyber Threat Landscape
PowerSploit has evolved significantly since its initial release, adapting to changes in security technologies and detection methods. Early versions focused primarily on penetration testing capabilities, but as security solutions improved, the framework incorporated additional features to evade detection. Modern versions of PowerSploit include techniques to bypass application whitelisting, obfuscate malicious code, and operate stealthily within compromised environments. This evolution reflects the ongoing arms race between security professionals and malicious actors in the cybersecurity landscape.
The widespread adoption of PowerSploit by various threat groups has led to its inclusion in numerous attack campaigns targeting organizations across different sectors. State-sponsored actors, cybercriminal groups, and ransomware operators have all incorporated PowerSploit into their attack arsenals due to its effectiveness and versatility. This broad adoption has prompted security vendors to develop specific detection mechanisms for PowerSploit activities, while also raising awareness among security professionals about the need for specialized monitoring strategies beyond traditional security solutions.
Network-Based Detection Methods
Network Traffic Analysis for PowerSploit
Network traffic analysis serves as a crucial first line of defense in detecting PowerSploit activities. By monitoring network communications for patterns indicative of PowerShell-based attacks, security teams can identify potential PowerSploit usage even before it reaches endpoints. PowerSploit modules often generate distinctive network traffic patterns when communicating with command and control servers or exfiltrating data. These patterns may include unusual DNS queries, atypical protocol usage, or connections to known malicious IP addresses.
Advanced network detection systems can analyze traffic metadata to identify suspicious PowerShell-related activities. For instance, PowerShell commands used by PowerSploit often result in specific network behaviors such as unusual TLS handshake patterns, abnormal data transfer sizes, or connections to unexpected ports. Security information and event management (SIEM) systems can correlate these network indicators with other security events to build a comprehensive picture of potential PowerSploit attacks. Implementing network traffic analysis tools specifically designed to detect PowerShell-based attacks can significantly enhance an organization’s ability to identify PowerSploit activities early in the attack lifecycle.
DNS Monitoring Techniques
DNS monitoring provides valuable insights into potential PowerSploit activities within an organization’s network. PowerSploit modules often generate unique DNS query patterns when establishing command and control communications or exfiltrating data. These may include unusually long domain names, high-frequency DNS queries to specific domains, or DNS requests to newly registered domains. Security teams can implement DNS monitoring solutions that analyze query patterns for anomalies indicative of PowerSploit usage.
Advanced DNS monitoring techniques include:
- Analyzing DNS query lengths for unusually long domain names often used in data exfiltration
- Monitoring DNS query frequencies to identify patterns consistent with command and control communications
- Tracking DNS requests to newly registered domains or domains with suspicious characteristics
- Implementing DNS sinkholing to redirect suspicious DNS queries to analysis systems
- Correlating DNS data with other security events to identify potential PowerSploit activities
Protocol Anomaly Detection
Protocol anomaly detection focuses on identifying unusual patterns in network protocol usage that may indicate PowerSploit activities. PowerSploit modules often leverage standard protocols in non-standard ways to evade detection or exfiltrate data. For example, attackers might use DNS tunnels, ICMP covert channels, or HTTP/S traffic in unusual patterns to communicate with compromised systems. These anomalies can be detected through careful analysis of protocol usage patterns.
Implementing protocol anomaly detection requires establishing baselines of normal network behavior and identifying deviations from these patterns. Security teams should monitor for unusual port usage, atypical packet sizes, or irregular timing in network communications. PowerSploit activities may generate distinctive protocol anomalies such as PowerShell commands embedded in web traffic, unusual encryption patterns, or atypical data transfer sequences. Advanced detection systems can leverage machine learning algorithms to identify subtle anomalies that might indicate PowerSploit usage, even when attackers attempt to blend their activities with normal network traffic.
Endpoint Detection Strategies
PowerShell Logging and Monitoring
PowerShell logging and monitoring represent critical components in detecting PowerSploit activities at the endpoint level. By enabling comprehensive PowerShell logging, organizations can capture detailed information about PowerShell command execution, script content, and module loading. Microsoft provides several PowerShell logging options including module logging, script block logging, and transcription, each offering different levels of visibility into PowerShell activities. These logging mechanisms can capture the specific commands and scripts used by PowerSploit modules, providing valuable evidence for detection and investigation.
Implementing PowerShell logging requires careful configuration to balance security visibility with performance considerations. Module logging captures information about cmdlet and function usage, while script block logging records the actual content of PowerShell scripts as they execute. PowerShell transcription creates a text-based record of all PowerShell sessions, providing comprehensive visibility into PowerSploit activities. Security teams should configure these logging options across all endpoints and forward the collected data to centralized logging systems for analysis. Regular review of PowerShell logs can reveal indicators of PowerSploit usage such as suspicious command patterns, unusual module imports, or script content consistent with known PowerSploit modules.
Windows Event Log Analysis
Windows Event Log analysis provides another valuable method for detecting PowerSploit activities on endpoints. PowerSploit operations generate specific event log entries that can indicate malicious PowerShell usage. Security teams should focus on events related to PowerShell execution, process creation, and security policy changes. Event IDs such as 4104 (PowerShell script block logging), 4688 (new process creation), and various security events can provide evidence of PowerSploit activities when properly analyzed.
Advanced event log analysis techniques include:
- Correlating PowerShell execution events with process creation events to identify suspicious command chains
- Analyzing event log sequences to identify patterns consistent with PowerSploit attack techniques
- Monitoring for specific event IDs associated with known PowerSploit modules and techniques
- Implementing automated alerting for suspicious PowerShell-related events
- Creating custom event log queries to identify potential PowerSploit activities across the enterprise
Process Creation Monitoring
Process creation monitoring focuses on detecting suspicious process execution patterns that may indicate PowerSploit activities. PowerSploit modules often spawn or manipulate processes in ways that can be detected through careful monitoring of process creation events. Security teams should implement comprehensive process monitoring that captures parent-child process relationships, command line arguments, and process execution paths. This information can reveal suspicious PowerShell usage patterns indicative of PowerSploit activities.
Advanced process monitoring techniques include analyzing process creation trees to identify unusual parent-child relationships, such as PowerShell being launched by Office applications or browsers. Monitoring for specific command line arguments associated with PowerSploit modules can also provide early detection of malicious activities. Security teams should implement process monitoring solutions that can detect encoded PowerShell commands, unusual execution flags, or suspicious parameter combinations often used by PowerSploit. By correlating process creation events with other security indicators, organizations can build a comprehensive picture of potential PowerSploit attacks and respond appropriately.
Memory Forensics Approaches
Memory Dump Analysis Techniques
Memory dump analysis represents a powerful approach to detecting PowerSploit activities that may not leave traces on disk. Since PowerSploit operates primarily in memory, traditional disk-based forensics may miss evidence of its usage. Memory forensics allows security professionals to examine the contents of RAM to identify PowerSploit modules, scripts, and artifacts that indicate malicious PowerShell activities. This approach can detect PowerSploit even when attackers employ techniques to avoid disk-based detection methods.
Advanced memory dump analysis techniques include scanning for PowerShell artifacts such as script blocks, modules, and runspaces that may contain PowerSploit code. Security professionals can use specialized memory forensics tools to extract PowerShell-related artifacts from memory dumps and analyze them for malicious content. Memory analysis can also reveal PowerSploit command history, variable contents, and execution context that provide valuable evidence for investigation. By implementing regular memory acquisition from critical systems and analyzing them for PowerSploit artifacts, organizations can detect attacks that might otherwise remain hidden from traditional security solutions.
Detecting PowerSploit in RAM
Detecting PowerSploit in RAM requires specialized techniques to identify PowerShell artifacts and malicious code patterns within memory. PowerSploit modules often leave distinctive signatures in memory that can be detected through careful analysis. Security professionals should look for PowerShell runspaces, script blocks, and module artifacts that contain PowerSploit code. Memory forensics can reveal PowerSploit activities even when attackers employ obfuscation techniques or attempt to hide their presence.
Advanced detection techniques include scanning memory for known PowerSploit function names, variable patterns, and code structures. Memory analysis can also detect PowerSploit injection techniques where malicious code is injected into legitimate processes. Security teams should implement memory scanning tools that can identify PowerShell-related artifacts and analyze them for malicious content. By examining memory regions associated with PowerShell processes, security professionals can uncover evidence of PowerSploit activities that might be missed by other detection methods. This approach is particularly valuable for detecting advanced PowerSploit usage that employs anti-forensic techniques to avoid detection.
Advanced Memory Forensics Tools
Advanced memory forensics tools provide specialized capabilities for detecting PowerSploit activities in memory. These tools offer features specifically designed to extract and analyze PowerShell artifacts from memory dumps. Security professionals should leverage tools such as Volatility with PowerShell-specific plugins, PowerForensics, or other specialized memory analysis frameworks to identify PowerSploit remnants in memory. These tools can extract PowerShell script blocks, runspaces, and module information that may contain evidence of PowerSploit usage.
Implementing advanced memory forensics requires specialized knowledge and tools but provides significant value in detecting sophisticated PowerSploit attacks. Security teams should develop procedures for acquiring memory images from critical systems and analyzing them for PowerSploit artifacts. Advanced tools can reconstruct PowerShell command histories, analyze script contents, and identify malicious modules even when attackers attempt to obfuscate their activities. By incorporating memory forensics into their detection strategies, organizations can significantly enhance their ability to detect PowerSploit attacks that operate primarily in memory and avoid traditional detection methods.
Behavioral Analysis Methods
User Behavior Analytics (UBA)
User Behavior Analytics (UBA) provides a powerful method for detecting PowerSploit activities by analyzing patterns of user behavior and identifying anomalies that may indicate malicious PowerShell usage. PowerSploit attacks often result in unusual user behavior patterns that can be detected through comprehensive behavioral analysis. Security teams should implement UBA solutions that monitor PowerShell usage patterns, command execution frequencies, and access patterns to identify potential PowerSploit activities.
Advanced UBA techniques include establishing baselines of normal PowerShell usage for each user and detecting deviations from these patterns. PowerSploit activities often generate distinctive behavioral patterns such as unusual command sequences, atypical PowerShell usage times, or abnormal access patterns. Security teams should implement machine learning-based UBA solutions that can identify subtle behavioral anomalies indicative of PowerSploit attacks. By correlating PowerShell usage with other behavioral indicators such as file access, network connections, and system modifications, organizations can build a comprehensive picture of potential PowerSploit activities and respond appropriately.
Anomaly Detection in System Activities
Anomaly detection in system activities focuses on identifying unusual patterns in system behavior that may indicate PowerSploit usage. PowerSploit modules often generate distinctive system activity patterns that can be detected through comprehensive monitoring and analysis. Security teams should implement anomaly detection solutions that monitor system events, process activities, and resource usage to identify potential PowerSploit attacks.
Key indicators of PowerSploit activities include:
- Unusual PowerShell execution patterns such as high-frequency command execution or atypical command sequences
- Anomalous process creation events where PowerShell is launched by unexpected parent processes
- Abnormal resource usage patterns associated with PowerShell processes
- Unusual file system access patterns such as accessing sensitive files through PowerShell
- Atypical network connection patterns originating from PowerShell processes
Command Line Argument Analysis
Command line argument analysis provides valuable insights into potential PowerSploit activities by examining PowerShell command execution patterns. PowerSploit modules often use distinctive command line arguments and parameter combinations that can be detected through careful analysis. Security teams should implement monitoring solutions that capture PowerShell command line arguments and analyze them for suspicious patterns indicative of PowerSploit usage.
Advanced command line analysis techniques include detecting encoded PowerShell commands, unusual parameter combinations, or suspicious argument patterns often used by PowerSploit modules. Security teams should implement solutions that can decode and analyze PowerShell command lines for malicious content even when attackers employ obfuscation techniques. By examining command execution frequency, parameter usage patterns, and argument sequences, organizations can identify potential PowerSploit activities that might otherwise remain hidden. Command line argument analysis should be combined with other detection methods to build a comprehensive defense against PowerSploit attacks.
Proactive Defense Measures
PowerShell Constrained Language Mode
PowerShell Constrained Language Mode represents a proactive defense measure that can significantly limit PowerSploit effectiveness by restricting PowerShell’s capabilities. This security feature restricts PowerShell to a constrained language mode that prevents execution of certain commands and operations commonly used by PowerSploit modules. By implementing constrained language mode across an organization’s endpoints, security teams can create a strong barrier against PowerSploit attacks while still allowing legitimate PowerShell usage for administrative tasks.
Implementing PowerShell Constrained Language Mode requires careful planning to ensure compatibility with legitimate business applications and administrative processes. Security teams should work with system administrators to identify necessary PowerShell functionalities and create application control policies that balance security with operational requirements. Constrained language mode can be enforced through group policies, system-wide configurations, or application whitelisting solutions. When properly implemented, this defense measure can significantly reduce the attack surface available to PowerSploit while maintaining necessary PowerShell functionality for legitimate business operations.
Application Whitelisting Strategies
Application whitelisting strategies provide another proactive defense measure against PowerSploit attacks by controlling which applications and scripts can execute on endpoints. By implementing comprehensive application whitelisting policies, organizations can prevent unauthorized PowerShell scripts and modules from executing, including those used by PowerSploit. This approach creates a strong defense against PowerSploit by ensuring that only approved PowerShell code can run on endpoints.
Advanced application whitelisting strategies include:
- Implementing PowerShell execution policies that restrict script execution to approved locations and publishers
- Creating publisher and hash-based rules for PowerShell scripts and modules
- Implementing AppLocker or similar application control solutions to manage PowerShell execution
- Using Windows Defender Application Control (WDAC) to create comprehensive code integrity policies
- Developing granular rules that allow legitimate PowerShell usage while blocking malicious activities
Threat Hunting Methodologies
Threat hunting methodologies represent a proactive approach to detecting PowerSploit activities by actively searching for indicators of compromise rather than waiting for automated alerts. Security teams should develop comprehensive threat hunting procedures specifically designed to identify PowerSploit usage within their environments. This proactive approach can detect PowerSploit attacks that may evade automated detection systems and provide early warning of potential security breaches.
Effective threat hunting for PowerSploit involves understanding the framework’s capabilities and developing hypotheses about how it might be used within the organization’s environment. Security teams should regularly hunt for PowerShell artifacts, unusual execution patterns, and other indicators of PowerSploit activities. This process should include examining system logs, memory captures, and network traffic for evidence of PowerSploit usage. By implementing regular threat hunting activities focused on PowerSploit detection, organizations can identify attacks early in their lifecycle and respond before significant damage occurs. Threat hunting should be integrated with other detection methods to create a comprehensive defense against PowerSploit attacks.
Conclusion
Detecting PowerSploit requires a multi-layered security approach combining network monitoring, endpoint detection, memory forensics, behavioral analysis, and proactive defense measures. Organizations must implement comprehensive PowerShell logging, network traffic analysis, and advanced threat hunting techniques to identify PowerSploit activities early. By understanding PowerSploit’s capabilities and implementing specialized detection strategies, security teams can significantly enhance their ability to detect and respond to these sophisticated attacks before critical damage occurs.