PowerSploit has emerged as a powerful tool in the cybersecurity landscape, raising questions about its legality and appropriate usage. This comprehensive PowerShell framework offers security professionals a suite of modules designed for penetration testing, post-exploitation, and security assessments. As organizations increasingly prioritize cybersecurity, understanding the legal boundaries surrounding such tools becomes crucial for professionals seeking to strengthen their security posture without crossing legal lines.
The legal status of PowerSploit exists in a gray area that depends heavily on intent, authorization, and jurisdiction. When used by cybersecurity professionals with proper authorization, PowerSploit serves as a legitimate security testing tool. However, the same capabilities that make it valuable for security testing also make it attractive to malicious actors. This dual-use nature creates complexity in determining legality, requiring careful consideration of context and compliance with applicable laws and regulations.
This article explores the legal implications of using PowerSploit across different scenarios, examining the frameworks that govern security testing tools, potential risks, and best practices for ensuring compliance. Whether you’re a cybersecurity professional, security researcher, or IT administrator, understanding these legal boundaries is essential for leveraging PowerSploit’s capabilities while maintaining ethical and legal standards in your security operations.
PowerSploit
What is PowerSploit?
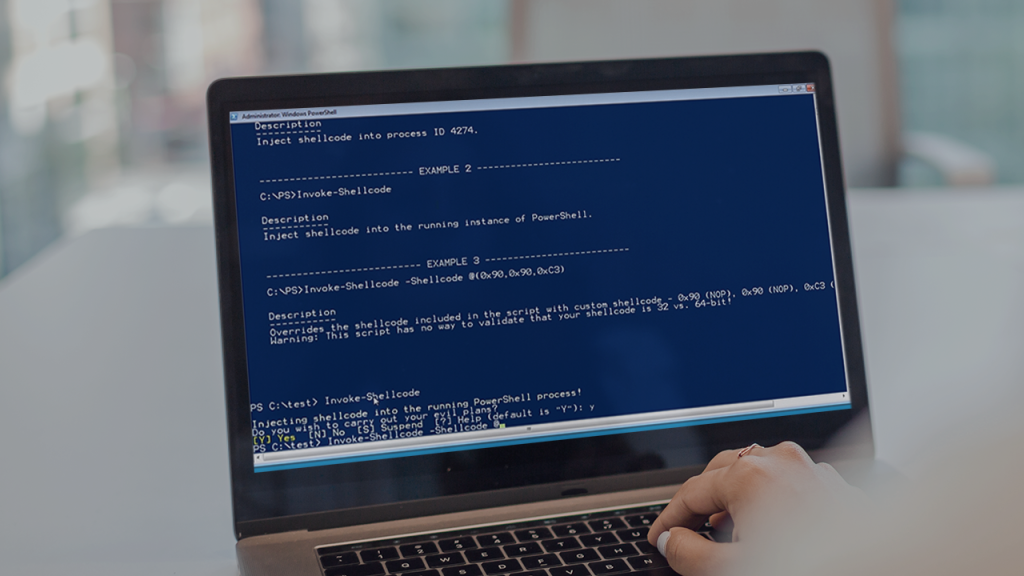
PowerSploit is a collection of PowerShell modules that aid penetration testers and security professionals in assessing the security posture of Windows systems. Developed originally as an open-source project, it provides a comprehensive toolkit for various security assessment tasks including reconnaissance, privilege escalation, persistence, and exfiltration. The tool leverages PowerShell’s deep integration with Windows to perform sophisticated security tests that can identify vulnerabilities and potential attack vectors.
The framework consists of multiple modules, each targeting specific aspects of security testing. These modules include capabilities for code execution, script modification, lateral movement, and data exfiltration. PowerSploit’s effectiveness stems from its ability to operate within legitimate Windows processes, making it difficult for traditional security solutions to detect its activities when used maliciously.
History and Development
PowerSploit was initially developed by security professionals to address the growing need for PowerShell-based security testing tools. As PowerShell became increasingly integrated into Windows administration, security researchers recognized its potential for both legitimate security testing and malicious exploitation. The project evolved through community contributions, with security professionals adding new modules and capabilities to address emerging threats and testing requirements.
The development of PowerSploit reflects the broader trend of offensive security tools becoming more sophisticated and accessible. Initially maintained as a standalone project, PowerSploit has undergone various ownership changes and forks as the cybersecurity landscape evolved. Its development history demonstrates how security tools often emerge from practical needs identified by professionals working in the field, rather than from formal development processes.
Key Components
PowerSploit consists of several key components, each serving specific security testing functions. The PowerUp module focuses on privilege escalation, helping identify misconfigurations that could allow users to gain elevated privileges. The PowerView module provides Windows domain reconnaissance capabilities, enabling testers to map network environments and identify potential attack paths. The Invoke-Mimikatz module integrates credential extraction capabilities, allowing security professionals to test credential protection mechanisms.
Other significant components include modules for persistence testing, which help organizations determine how well they can detect attackers attempting to maintain access to compromised systems. The framework also includes modules for script modification and code execution, enabling security professionals to test application whitelisting and other security controls. These components work together to provide a comprehensive toolkit for Windows security assessments.
Legal Framework for Security Tools
Laws Governing Security Testing
The legality of using PowerSploit falls under various computer crime laws that differ significantly across jurisdictions. In the United States, the Computer Fraud and Abuse Act (CFAA) establishes the primary legal framework for unauthorized computer access. Under the CFAA, using PowerSploit without explicit authorization could potentially constitute illegal computer intrusion, regardless of intent. Similar laws exist in other countries, such as the UK’s Computer Misuse Act and the EU’s Directive on Attacks against Information Systems.
These laws generally focus on unauthorized access rather than the specific tools used, meaning the legality of PowerSploit depends on whether you have permission to test the target systems. Many jurisdictions have carved out exceptions for security testing conducted with proper authorization, but these exceptions often require specific documentation and adherence to established protocols. Understanding the relevant laws in your jurisdiction is essential before using PowerSploit in any capacity.
Jurisdictional Differences
Legal standards for security testing tools vary significantly across different countries and even between states or provinces within countries. Some jurisdictions have more permissive approaches to security testing, allowing broader interpretation of authorization, while others maintain strict regulations that could criminalize certain testing activities even with good intentions. These jurisdictional differences create complexity for security professionals working across geographic boundaries or in cloud environments where data and systems might span multiple legal frameworks.
International organizations must navigate these jurisdictional variations carefully, as actions legal in one country might violate laws in another. This is particularly challenging for penetration testers and security consultants who work with clients across different regions. The global nature of cybersecurity threats has prompted some harmonization of laws, but significant differences remain that require careful consideration when using tools like PowerSploit in international contexts.
Compliance Requirements
Beyond criminal laws, various regulatory frameworks impose additional requirements on security testing activities. Industries such as finance, healthcare, and critical infrastructure often have specific compliance standards that govern how security assessments must be conducted. These requirements may include documentation of authorization, scope limitations, reporting protocols, and data protection measures during testing activities.
Compliance frameworks like PCI DSS for payment card security, HIPAA for healthcare information, and GDPR for European data protection all include provisions that impact how security testing can be performed. Organizations using PowerSploit must ensure their testing procedures align with these regulatory requirements to avoid compliance violations that could result in significant penalties. This often involves implementing additional controls and documentation beyond what might be required by law alone.
Ethical Use Cases
Penetration Testing
PowerSploit serves as a valuable tool in authorized penetration testing engagements where security professionals simulate attacks to identify vulnerabilities. In these contexts, the tool helps testers evaluate the effectiveness of security controls and demonstrate potential impacts of real attacks. Penetration testers use PowerSploit to assess Windows environments comprehensively, testing for privilege escalation opportunities, lateral movement possibilities, and data exfiltration risks that might not be apparent through other testing methods.
Professional penetration testers typically follow established methodologies like PTES (Penetration Testing Execution Standard) or NIST SP 800-115 when using tools like PowerSploit. These frameworks emphasize proper scoping, authorization documentation, and responsible disclosure of findings. When used within these professional boundaries, PowerSploit enables more thorough assessments that ultimately help organizations improve their security posture rather than cause harm.
Security Research
Security researchers utilize PowerSploit to study attack techniques and develop defensive measures against emerging threats. By understanding how offensive tools operate, researchers can create more effective detection methods and mitigation strategies. This research often involves testing PowerSploit against various security configurations to identify which controls are effective and which might require improvement.
Research use of PowerSploit typically occurs in controlled laboratory environments with isolated systems designed specifically for security research. Researchers document their findings and often share them with the broader security community through publications, conference presentations, or blog posts. This knowledge sharing helps advance the field of cybersecurity by improving collective understanding of attack techniques and defensive measures.
Educational Purposes
Educational institutions and training programs incorporate PowerSploit into cybersecurity curricula to teach students about offensive security techniques and defensive countermeasures. In these educational contexts, students learn how attackers might leverage PowerShell capabilities and how defenders can detect and mitigate such activities. This hands-on experience helps develop the next generation of cybersecurity professionals with practical knowledge of real-world attack techniques.
Educational use of PowerSploit occurs in controlled environments specifically designed for learning, such as virtual labs or dedicated training systems. Students typically must complete prerequisite coursework on ethics and legal requirements before working with offensive tools. This educational approach ensures that future security professionals understand both the technical capabilities of tools like PowerSploit and the ethical responsibilities that come with using them.
Risks and Consequences
Legal Penalties
Unauthorized use of PowerSploit can result in severe legal consequences including criminal charges, fines, and imprisonment. Under laws like the CFAA, individuals convicted of unauthorized computer access face significant penalties that escalate based on factors such as damage caused, data stolen, and systems compromised. Even well-intentioned security testing without proper authorization can lead to legal action, as courts generally focus on unauthorized access rather than intent when determining criminal liability.
Civil liability represents another significant risk, as organizations affected by unauthorized testing may sue for damages, business disruption, or other harms. These civil cases can result in substantial financial judgments beyond any criminal penalties. The legal costs associated with defending against such charges can be devastating even for individuals ultimately found not guilty, making proper authorization essential before using PowerSploit in any testing scenario.
Professional Repercussions
Beyond legal consequences, misuse of PowerSploit can severely impact professional careers and reputations. Security professionals found to have used testing tools without authorization may face termination from employment, difficulty finding future positions, and damage to professional standing within the cybersecurity community. Industry certifications like CISSP, CEH, or OSCP could be revoked for ethical violations, significantly impacting career prospects.
Professional organizations within cybersecurity often have codes of ethics that explicitly prohibit unauthorized testing. Violation of these ethical standards can result in expulsion from professional associations and being blacklisted within the industry. The cybersecurity community is relatively small and well-connected, meaning reputation damage from ethical violations can have long-lasting career impacts that extend far beyond the immediate consequences of any single incident.
Organizational Impact
When employees misuse tools like PowerSploit, the resulting consequences extend beyond individuals to affect their entire organizations. Companies may face regulatory penalties, loss of customer trust, and damage to brand reputation if their employees are found conducting unauthorized security testing. These impacts can be particularly severe for organizations in regulated industries or those handling sensitive customer data.
Organizational consequences also include potential disruption to business operations during investigations into unauthorized testing activities. Companies may need to conduct internal investigations, cooperate with law enforcement, and implement additional security controls to prevent future incidents. These activities divert resources from business objectives and can impact productivity across the organization. Additionally, organizations may face increased insurance premiums or difficulty obtaining cybersecurity coverage following incidents involving misuse of security testing tools.
Best Practices for Legal Use
Authorization Documentation
Proper authorization documentation represents the foundation for legal use of PowerSploit. This documentation should clearly define the scope of testing, including specific systems, networks, and timeframes for testing activities. Authorization should be obtained in writing from individuals with appropriate authority within the target organization, typically senior IT leadership or designated security officers. The authorization should explicitly mention the use of PowerSploit or similar tools to avoid ambiguity about permitted activities.
The authorization document should include contact information for both the testing team and organizational representatives who can be reached during the engagement. It should also establish protocols for stopping testing immediately if unexpected issues arise. Organizations often develop standardized authorization templates to ensure all necessary elements are included and to maintain consistency across different testing engagements. These templates help protect both the testing organization and the client by clearly establishing the legal parameters for testing activities.
Scope Limitation
Clearly defining and adhering to scope limitations is essential for legal use of PowerSploit. The testing scope should specify exactly which systems, applications, and networks are included in the assessment, along with any explicitly excluded areas. Testers must maintain strict adherence to these boundaries, avoiding any testing activities outside the defined scope regardless of potential security findings that might exist in excluded areas.
Time limitations represent another critical aspect of scope definition, with testing activities restricted to specific dates and times to minimize business impact. PowerSploit usage should also be limited to the specific techniques and modules necessary to achieve the testing objectives. Testers should document any instances where they encounter systems outside the defined scope but must not attempt to test these systems without explicit authorization expansion. This disciplined approach to scope management helps ensure testing remains within legal boundaries while still providing valuable security insights.
Reporting Protocols
Establishing clear reporting protocols is essential for legal and ethical use of PowerSploit. Testers should implement structured processes for documenting findings, including both successful exploits and failed attempts. This documentation should include timestamps, specific commands executed (using PowerSploit modules), system responses, and any potential impacts observed. Regular status reports should be provided to the designated organizational contacts throughout the testing engagement.
Critical findings that pose immediate risk should be communicated through established escalation channels as soon as they’re discovered. At the conclusion of testing, a comprehensive report should detail all findings, their potential business impact, and recommended remediation steps. This report should include specific details about PowerSploit usage to help organizations understand how the vulnerabilities were discovered and potentially detected. The reporting process should maintain appropriate confidentiality of sensitive information discovered during testing while providing sufficient detail for effective remediation.
Alternatives to PowerSploit
Open Source Options
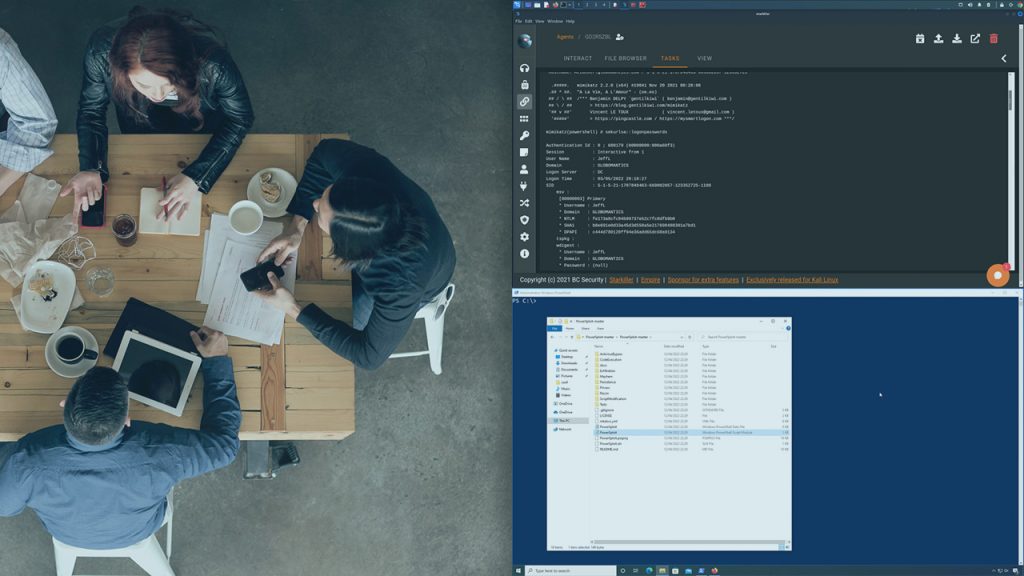
Several open-source alternatives to PowerSploit offer similar capabilities for Windows security testing. Empire is a popular PowerShell post-exploitation framework that provides extensive capabilities for security assessments. Cobalt Strike, while partially commercial, offers some open-source components and has become an industry standard for advanced penetration testing. These alternatives often provide different interfaces or approaches to similar security testing functions, allowing security professionals to choose tools that best fit their testing methodologies and technical preferences.
Other open-source options include Powercat, a PowerShell implementation of Netcat for network testing, and Inveigh, a PowerShell tool for Windows network penetration testing. These tools often focus on specific aspects of security testing rather than providing the comprehensive framework of PowerSploit. Security professionals may use combinations of these specialized tools to achieve similar results to PowerSploit while potentially avoiding certain detection signatures or compliance concerns associated with more widely known tools.
Commercial Solutions
Commercial security testing platforms offer alternatives to PowerSploit with additional features, support, and compliance documentation. Tools like Core Impact, Canvas, and Metasploit Pro provide comprehensive penetration testing capabilities with user-friendly interfaces and reporting features. These commercial solutions typically include built-in authorization templates, scope management tools, and detailed reporting capabilities that can help ensure testing activities remain within legal and compliance boundaries.
The advantage of commercial solutions often lies in their professional support, regular updates, and documentation of testing methodologies for compliance purposes. While these tools typically require financial investment, they may reduce legal risks through more structured approaches to testing and comprehensive audit trails. Organizations with significant compliance requirements or limited in-house security expertise often find commercial solutions provide appropriate risk mitigation for their security testing needs.
Custom Development
Some organizations choose to develop custom security testing tools rather than using PowerSploit or other publicly available options. Custom development allows organizations to tailor tools specifically to their environments, compliance requirements, and testing methodologies. This approach can provide more control over how testing tools operate and what data they collect, potentially reducing privacy and compliance concerns.
Custom tool development requires significant technical expertise and ongoing maintenance to remain effective against evolving security controls. Organizations pursuing this approach must ensure their custom tools include appropriate logging, scope limitations, and safety mechanisms to prevent unintended impacts during testing. While resource-intensive, custom development can result in testing tools that precisely match organizational requirements while potentially avoiding detection signatures associated with widely used tools like PowerSploit.
Conclusion
PowerSploit exists in a complex legal landscape where authorization, intent, and jurisdiction determine its legality. When used with proper authorization for legitimate security testing, research, or educational purposes, PowerSploit serves as a valuable tool for improving cybersecurity. However, unauthorized use can result in severe legal penalties, professional consequences, and organizational impacts. Security professionals must prioritize proper authorization documentation, scope limitation, and responsible disclosure when utilizing this powerful framework.