PowerSploit stands as a powerful collection of PowerShell modules designed for penetration testing, security assessments, and post-exploitation activities. Developed originally for security professionals and ethical hackers, this toolkit has gained significant popularity in the cybersecurity landscape due to its versatility and effectiveness. PowerSploit leverages the native capabilities of PowerShell to provide a comprehensive suite of tools that can be used for various security-related tasks, making it an indispensable resource for security teams worldwide.
The framework was created with the primary goal of assisting security professionals in identifying vulnerabilities, testing security controls, and simulating real-world attack scenarios. By utilizing PowerShell’s inherent capabilities, PowerSploit can execute complex tasks with minimal footprint, making it particularly effective in environments where traditional security tools might be detected or blocked. Its modular design allows users to select specific components based on their testing requirements, providing flexibility and customization options that cater to diverse security assessment needs.
PowerSploit Basics
What is PowerSploit?
PowerSploit is a comprehensive PowerShell-based penetration testing framework that provides security professionals with a wide array of tools for security assessments. The toolkit is specifically designed to leverage PowerShell’s capabilities for executing various security-related tasks, including reconnaissance, privilege escalation, persistence, and exfiltration. PowerSploit’s modular architecture allows users to selectively employ components based on their specific testing requirements, making it a versatile solution for diverse security scenarios.
PowerSploit’s modules are organized into distinct categories based on their functionality, including code execution, script modification, persistence, reconnaissance, and exfiltration. Each category contains specialized tools designed to perform specific tasks within the security assessment process. The framework’s open-source nature ensures continuous improvement and adaptation to address evolving security threats and defensive measures.
History and Development
PowerSploit emerged in the early 2010s as PowerShell gained prominence as both a system administration tool and a potential security vector. Matthew Graeber, a security researcher, recognized the potential of PowerShell for offensive security operations and began developing a collection of modules that could leverage its capabilities. The initial versions focused on code execution and memory manipulation techniques, addressing the growing need for tools that could operate stealthily within Windows environments.
The development of PowerSploit has been influenced by the changing nature of cybersecurity threats and the increasing sophistication of both offensive and defensive security techniques. Microsoft’s implementation of enhanced security measures in PowerShell, such as Constrained Language Mode and Script Block Logging, has necessitated continuous adaptation of PowerSploit’s methodologies. This ongoing evolution ensures that PowerSploit remains relevant and effective in the face of advancing security controls and detection mechanisms.
Core Components
PowerSploit’s architecture is built around several core components that provide distinct functionalities for security testing. The Code Execution module enables users to execute arbitrary code on target systems, bypassing security restrictions and maintaining stealth during operations. This component includes techniques for DLL injection, reflective PE loading, and shellcode execution, providing multiple avenues for running code in memory without writing to disk.
The Reconnaissance module provides tools for gathering information about target systems and networks. This component includes capabilities for network mapping, credential harvesting, and system enumeration. The Exfiltration module complements the reconnaissance capabilities by offering secure methods for extracting data from target environments while minimizing detection risks. These core components work together to provide a comprehensive toolkit for security assessments across all phases of penetration testing.
Installation and Setup
Prerequisites
Before installing PowerSploit, several prerequisites must be addressed to ensure optimal functionality. A Windows system with PowerShell version 2.0 or higher is required, though newer versions are recommended for enhanced capabilities and security features. Administrative privileges are necessary for certain modules to function correctly, particularly those involving system modification or privilege escalation.
Network connectivity is essential for downloading PowerSploit and potentially for certain modules that require external communication. For organizations with strict security controls, proper authorization must be obtained before installing and using PowerSploit to ensure compliance with security policies and legal requirements. Users should also familiarize themselves with PowerShell fundamentals to effectively utilize PowerSploit’s capabilities.
Installation Steps
The installation process for PowerSploit is straightforward and can be completed through several methods. The most common approach involves cloning the PowerSploit repository from GitHub using the following command: git clone https://github.com/PowerShellMafia/PowerSploit.git. This method ensures that users obtain the latest version of the framework with all available modules and documentation.
After obtaining the PowerSploit files, users must import the modules into their PowerShell session using the Import-Module cmdlet. This can be done for individual modules or for the entire PowerSploit framework. To verify successful installation, users can run Get-Module to list the imported PowerSploit modules. It’s recommended to test basic functionality with simple commands to ensure proper installation before proceeding with security assessments.
Initial Configuration
Customizing the PowerShell profile to automatically load PowerSploit modules can streamline workflow for frequent users. This can be achieved by adding Import-Module commands to the PowerShell profile script. However, this approach should be used judiciously, as automatically loading security tools may introduce unnecessary risks in certain environments.
For organizations using PowerSploit across multiple systems, centralized configuration management can ensure consistency and compliance with security policies. This may involve creating standardized installation procedures, implementing version control for PowerSploit modules, and establishing guidelines for appropriate usage. Documenting custom configurations and modifications is essential for maintaining security and troubleshooting issues that may arise during operation.
PowerSploit Modules Overview
Code Execution Module
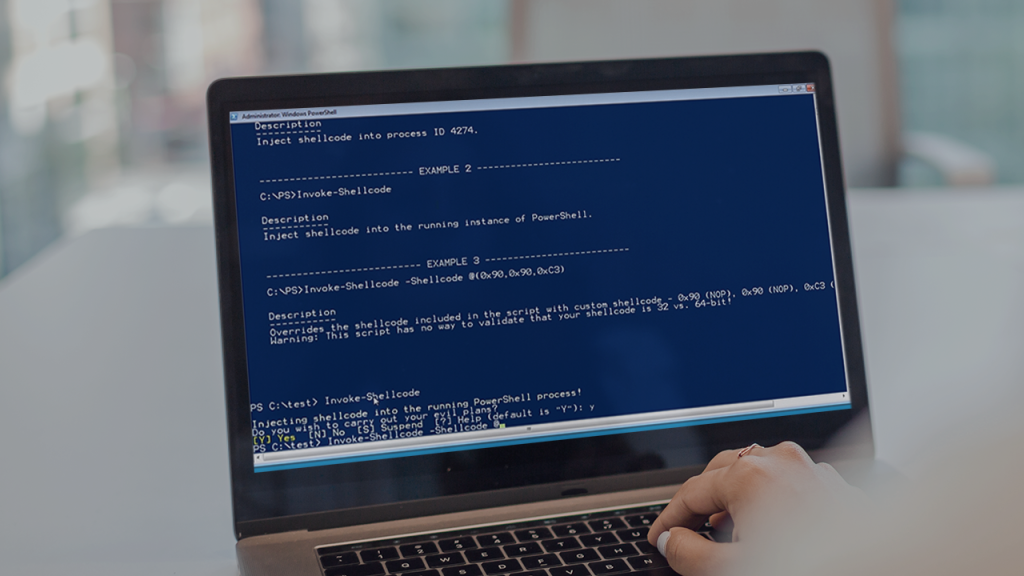
The Code Execution module represents one of PowerSploit’s most powerful components, enabling security professionals to execute arbitrary code on target systems. This module provides various techniques for bypassing security controls and running code in memory, minimizing forensic evidence. The Invoke-Shellcode function, for instance, allows users to execute shellcode within the PowerShell process without writing to disk, making detection significantly more challenging.
The Code Execution module incorporates multiple evasion techniques designed to bypass common security controls and detection mechanisms. These include AMSI bypass methods, PowerShell logging evasion, and memory allocation strategies that avoid detection by security software. Understanding these techniques is crucial for both offensive security professionals conducting authorized assessments and defenders seeking to improve their detection capabilities.
Persistence Module
One notable function within this module is New-UserPersistenceOption, which allows users to customize persistence mechanisms based on target environment characteristics. This flexibility enables security professionals to select the most appropriate persistence technique for specific scenarios, balancing stealth with reliability. The module also includes functions for detecting and removing persistence mechanisms, which can be valuable for cleanup activities after security assessments.
The Persistence module incorporates techniques for establishing privileged access through various Windows mechanisms, including WMI event subscriptions, service creation, and registry modifications. Each method has distinct advantages and detection profiles, allowing security professionals to select the most appropriate approach based on their specific testing requirements and the target environment’s security controls.
Reconnaissance Module
The Reconnaissance module in PowerSploit equips security professionals with tools for gathering comprehensive information about target systems and networks. This module includes capabilities for network mapping, credential harvesting, and system enumeration, providing valuable intelligence for subsequent security assessment phases. The Invoke-PortScan function, for example, enables users to identify open ports and services on target systems, forming the foundation for further exploitation attempts.
The Reconnaissance module also includes tools for Active Directory enumeration, enabling security professionals to map domain structures, identify privileged accounts, and gather information about group memberships and organizational units. These capabilities are particularly valuable for assessing the security of Windows-based enterprise environments and identifying potential attack paths that could be leveraged by malicious actors.
Common Use Cases
Penetration Testing
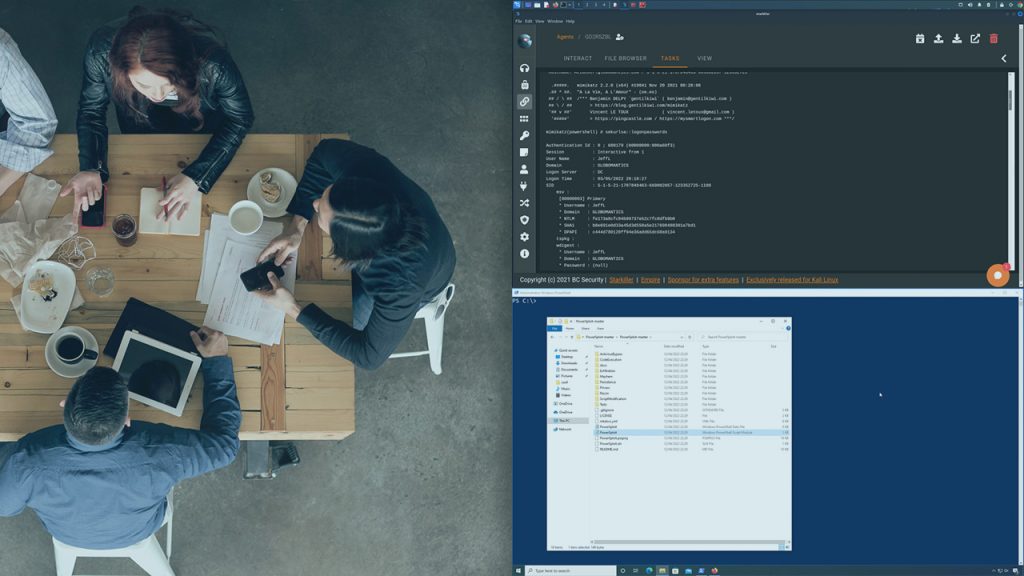
During penetration testing engagements, PowerSploit can be used to identify misconfigurations, weak security controls, and potential attack paths that malicious actors could exploit. The framework’s reconnaissance capabilities help testers gather critical information about target environments, while its code execution and persistence modules enable simulation of advanced attack techniques. This comprehensive approach allows organizations to identify vulnerabilities across multiple attack vectors and implement appropriate remediation measures.
Penetration testers often combine PowerSploit with other security tools to create customized testing methodologies tailored to specific environments or compliance requirements. The framework’s modular design allows for seamless integration with existing penetration testing workflows, enhancing the efficiency and effectiveness of security assessments. By simulating realistic attack scenarios, PowerSploit helps organizations understand their true security posture and prioritize remediation efforts based on actual risk levels.
Security Auditing
Security auditors leverage PowerSploit to evaluate the effectiveness of existing security controls and identify potential gaps in an organization’s defenses. The framework’s comprehensive capabilities enable auditors to test various security aspects, including access controls, authentication mechanisms, and data protection measures. By simulating attack techniques used by malicious actors, auditors can provide realistic assessments of an organization’s security posture and identify areas requiring improvement.
Security auditors often use PowerSploit to assess the resilience of an organization’s defenses against sophisticated attack techniques. By testing detection and response capabilities using PowerSploit’s evasion methods, auditors can identify weaknesses in security monitoring and incident response processes. This information helps organizations improve their security posture by addressing not only technical vulnerabilities but also procedural and operational gaps in their security programs.
Incident Response
During incident response activities, PowerSploit can be used to analyze malware behavior, identify persistence mechanisms, and trace attacker activities within compromised environments. The framework’s modules for code analysis and memory examination enable responders to understand malicious code functionality without executing it, reducing the risk of further compromise. This information is crucial for developing effective containment and eradication strategies.
Incident responders also leverage PowerSploit to validate the effectiveness of their remediation activities and ensure that attackers have been completely removed from compromised environments. By using the same techniques that malicious actors might employ, responders can verify that all persistence mechanisms have been identified and eliminated. This thorough approach helps prevent reinfection and ensures that security incidents are completely resolved rather than simply addressing the most visible symptoms.
Best Practices
Ethical Usage Guidelines
Ethical usage of PowerSploit is paramount for maintaining professional integrity and avoiding legal complications. Security professionals must obtain explicit authorization before deploying PowerSploit in any environment, ensuring that all testing activities comply with organizational policies and legal requirements. Documentation of authorization, scope, and limitations is essential for demonstrating compliance and protecting both the security professional and the organization from potential liability.
Regular communication with stakeholders throughout the testing process is essential for maintaining transparency and addressing concerns that may arise. Security professionals should document all PowerSploit usage, including specific modules employed, commands executed, and results obtained. This documentation not only demonstrates accountability but also provides valuable information for remediation activities and future security assessments.
Security Considerations
PowerSploit modules should be carefully vetted before use, particularly in sensitive environments. The open-source nature of the framework means that community-contributed modules may vary in quality and security. Security professionals should review code and understand functionality before deploying modules, particularly those that interact with critical systems or sensitive data. This due diligence helps prevent potential security vulnerabilities or unintended consequences from poorly implemented modules.
Access to PowerSploit should be strictly controlled and monitored to prevent unauthorized usage. Security professionals should store PowerSploit in secure locations with appropriate access controls and maintain logs of when and how the framework is used. In environments where PowerSploit is used for legitimate security purposes, implementing detection mechanisms for unauthorized usage can help prevent malicious actors from exploiting the same tools for nefarious purposes.
Maintaining Stealth
PowerSploit’s effectiveness often depends on its ability to operate stealthily within target environments. Security professionals should implement various techniques to minimize detection during authorized assessments, including using alternative execution methods, modifying command signatures, and leveraging legitimate system processes. These stealth techniques not only make assessments more realistic but also help organizations identify gaps in their detection capabilities.
Memory-based execution techniques should be preferred over file-based operations when possible, as they leave minimal forensic evidence and are more difficult to detect by traditional security tools. PowerSploit’s capabilities for reflective loading and in-memory execution can be particularly effective for maintaining stealth during security assessments. However, security professionals should balance stealth requirements with the need for comprehensive documentation of their activities.
Future of PowerSploit
Development Roadmap
The future development of PowerSploit continues to focus on enhancing capabilities while adapting to evolving security landscapes. Developers are working on new modules that address emerging attack techniques and defensive technologies, ensuring that PowerSploit remains relevant for security assessments. Enhanced evasion techniques are being developed to counter advanced detection mechanisms, particularly those leveraging machine learning and behavioral analysis.
The development roadmap also emphasizes improved usability and documentation to make PowerSploit more accessible to security professionals with varying levels of PowerShell expertise. Enhanced user interfaces, simplified command structures, and comprehensive tutorials are being developed to lower the barrier to entry while maintaining the framework’s powerful capabilities. These improvements aim to expand PowerSploit’s user base while preserving its advanced functionality for experienced security professionals.
Community Contributions
PowerSploit’s open-source nature ensures that community contributions will continue to play a vital role in its evolution. Security professionals worldwide contribute new modules, enhance existing functionality, and identify potential vulnerabilities or improvements. This collaborative approach ensures that PowerSploit remains at the forefront of offensive security tools, incorporating diverse perspectives and expertise from the global security community.
The PowerSploit community continues to develop educational resources, including tutorials, case studies, and best practice guides, to help security professionals effectively utilize the framework. These community-driven knowledge-sharing initiatives complement the technical development of PowerSploit, ensuring that users can maximize its value while maintaining ethical standards and security best practices.
Potential Challenges
PowerSploit faces several challenges as the cybersecurity landscape continues to evolve. Enhanced security controls in modern Windows environments, including stricter PowerShell policies and improved monitoring capabilities, require continuous adaptation of PowerSploit’s techniques. Microsoft’s focus on securing PowerShell against misuse presents an ongoing challenge for PowerSploit developers, who must find innovative ways to maintain functionality while respecting legitimate security improvements.
The increasing sophistication of detection technologies, including those powered by artificial intelligence and machine learning, presents another significant challenge for PowerSploit. These advanced detection mechanisms can identify subtle patterns and anomalies that traditional security tools might miss, requiring PowerSploit to develop more sophisticated evasion techniques. This cat-and-mouse game between offensive tools and defensive technologies will likely continue to intensify in the coming years.
Conclusion
PowerSploit continues to evolve as a powerful framework for security professionals conducting penetration tests, security audits, and incident response activities. Its comprehensive capabilities, modular design, and active community development ensure that it remains relevant in the ever-changing cybersecurity landscape.