PowerSploit represents a sophisticated collection of PowerShell modules designed specifically for penetration testing and red team operations. This powerful toolkit has gained significant attention in cybersecurity circles due to its advanced capabilities in post-exploitation activities. Security professionals frequently utilize PowerSploit to assess network vulnerabilities, while malicious actors may leverage its features to bypass traditional security measures. Understanding the relationship between PowerSploit and antivirus systems has become increasingly crucial for organizations seeking to strengthen their defensive postures against evolving threats.
The fundamental question of whether PowerSploit can bypass antivirus software requires a nuanced understanding of both technologies. Antivirus solutions have evolved significantly over the years, incorporating advanced detection mechanisms such as heuristic analysis, behavioral monitoring, and machine learning algorithms. However, PowerSploit’s PowerShell-based nature presents unique challenges for traditional security solutions, as PowerShell is a legitimate Windows administration tool that attackers can weaponize. This dual-use characteristic creates a complex cat-and-mouse game between offensive security tools leveraging PowerSploit and defensive solutions attempting to detect its malicious activities.
PowerSploit Architecture
PowerSploit’s modular architecture represents a sophisticated approach to penetration testing, offering security professionals a comprehensive toolkit for various attack scenarios. The framework consists of multiple PowerShell modules, each designed to perform specific tasks during different phases of an engagement. This modular design allows penetration testers to selectively employ components based on their requirements, making PowerSploit both versatile and efficient in real-world security assessments.
The technical foundation of PowerSploit leverages PowerShell’s inherent capabilities while extending them with specialized functions for offensive security operations. PowerShell’s integration with the Windows operating system provides deep access to system components, making it an ideal platform for security testing tools. PowerSploit capitalizes on this integration by creating modules that can interact with system APIs, manipulate memory, execute code in various contexts, and perform other advanced operations typically associated with sophisticated attack techniques.
Core Components of PowerSploit
PowerSploit’s modular structure encompasses several key components, each serving distinct purposes in penetration testing scenarios. These modules work together to provide comprehensive capabilities for security assessments, from initial access to post-exploitation activities. The framework’s design philosophy emphasizes flexibility and extensibility, allowing security professionals to customize their approach based on specific engagement requirements and target environments.
Persistence mechanisms within PowerSploit allow security professionals to maintain access to compromised systems across reboots and credential changes. These techniques simulate how real attackers establish long-term presence within networks, providing valuable insights into potential security gaps. The toolkit offers various persistence methods, from registry modifications to scheduled tasks, each with different stealth characteristics and detection challenges.
Technical Implementation Details
PowerSploit’s implementation leverages PowerShell’s object-oriented nature and .NET framework integration to create powerful security testing capabilities. The toolkit’s modules utilize Windows API calls through PowerShell’s native interoperability features, enabling direct interaction with system components. This approach allows PowerSploit to perform sophisticated operations that typically require lower-level programming languages, all within the PowerShell environment
PowerSploit’s modules often employ obfuscation techniques to avoid detection by security solutions. These techniques range from simple string encoding to more sophisticated methods like AMSI (Antimalware Scan Interface) bypassing. The toolkit’s developers continuously update these techniques to address new detection mechanisms implemented by antivirus and endpoint protection solutions, ensuring PowerSploit remains effective against evolving security controls.
Evolution and Development History
PowerSploit’s development history demonstrates the ongoing arms race between offensive security tools and defensive solutions. As antivirus and endpoint protection vendors improved their detection capabilities for PowerShell-based attacks, PowerSploit’s developers introduced new techniques to maintain effectiveness. This iterative process has led to increasingly sophisticated methods for bypassing security controls while maintaining the toolkit’s usability and reliability for legitimate security testing purposes.
The community-driven nature of PowerSploit’s development has contributed significantly to its effectiveness and relevance. Security professionals from diverse backgrounds contribute to the project, bringing insights from various industries and threat landscapes. This collaborative approach ensures that PowerSploit remains current with emerging attack techniques and defensive technologies, making it a valuable resource for organizations seeking to improve their security posture through realistic testing scenarios.
Antivirus Detection Mechanisms
Signature-based detection remains a foundational component of antivirus protection, though its effectiveness against tools like PowerSploit is limited due to the toolkit’s legitimate nature and customizable code. Modern antivirus solutions supplement this approach with heuristic analysis, which identifies potentially suspicious behaviors and code patterns rather than relying solely on known signatures. This behavioral approach is more effective against PowerSploit, as it can detect malicious activities even when the underlying code appears legitimate.
Advanced endpoint protection solutions incorporate additional detection layers such as machine learning models, memory scanning, and script analysis. These technologies examine the context and behavior of PowerShell scripts, looking for indicators of malicious intent even when the actual code may not match known threat signatures. The integration of these multiple detection approaches creates a more comprehensive defense against PowerShell-based attacks like those facilitated by PowerSploit.
Signature-Based Detection Limitations
The dynamic nature of PowerShell scripting further complicates signature-based detection approaches. PowerSploit modules can be easily modified, encoded, or obfuscated without changing their fundamental functionality, creating countless variations that would each require a unique signature for detection. This flexibility makes it impractical for antivirus vendors to maintain comprehensive signature coverage for all possible PowerSploit variations, leading to potential blind spots in protection.
PowerSploit’s legitimate use in security testing and administration creates additional challenges for signature-based detection. Many organizations utilize PowerSploit or similar tools for legitimate security assessments, meaning that simple detection of PowerSploit code may not indicate malicious activity. This context dependency requires more sophisticated detection approaches that can differentiate between authorized testing and unauthorized use, a capability that traditional signature-based detection lacks.
Heuristic and Behavioral Analysis
PowerSploit’s sophisticated techniques often trigger behavioral heuristics designed to identify advanced attack patterns. For example, the toolkit’s memory manipulation capabilities, code injection methods, and privilege escalation techniques typically deviate from normal administrative PowerShell usage, making them detectable through behavioral analysis. These heuristics can identify potentially malicious activities even when the specific PowerSploit implementation is unknown or customized.
The effectiveness of heuristic analysis against PowerSploit depends on the sophistication of the implemented detection rules and the balance between security coverage and false positives. Advanced endpoint protection solutions employ machine learning models trained on vast datasets of both legitimate and malicious PowerShell activities, allowing them to identify subtle patterns indicative of PowerSploit usage. These models can adapt to new attack techniques over time, providing more robust protection against evolving threats.
Advanced Detection Technologies
Modern antivirus solutions incorporate advanced detection technologies specifically designed to address PowerShell-based threats like PowerSploit. These technologies include AMSI (Antimalware Scan Interface) integration, which allows security solutions to inspect PowerShell scripts at runtime before execution. AMSI provides visibility into script content even when obfuscated or encoded, making it more difficult for PowerSploit modules to evade detection through traditional obfuscation techniques.
Cloud-based analysis and threat intelligence integration enhance detection capabilities by leveraging global security data to identify emerging PowerSploit usage patterns. These systems can detect novel attack techniques by correlating suspicious PowerShell activities across multiple environments, identifying potential threats that might not match known signatures or heuristics. This collective intelligence approach provides more comprehensive protection against PowerSploit and similar tools, particularly when combined with local detection mechanisms.
PowerSploit Evasion Techniques
PowerSploit incorporates various evasion techniques designed to bypass or delay detection by security solutions, reflecting the sophisticated nature of modern attack methodologies. These techniques range from simple obfuscation methods to advanced approaches that exploit legitimate system features to avoid triggering security alerts. Understanding these evasion capabilities provides valuable insights into potential security gaps and the challenges faced by antivirus solutions in detecting PowerShell-based threats.
The toolkit’s evasion capabilities are continuously updated to address new detection mechanisms implemented by security vendors. This ongoing evolution ensures that PowerSploit remains effective against emerging security controls while maintaining its utility for legitimate security testing purposes. The cat-and-mouse dynamic between PowerSploit’s evasion techniques and antivirus detection capabilities highlights the importance of multi-layered security approaches that don’t rely solely on any single detection method.
Obfuscation and Encoding Methods
PowerSploit employs various obfuscation techniques to conceal its code and functionality from basic security scanning methods. These techniques range from simple string manipulation to more sophisticated approaches that restructure the code’s logic while maintaining its functionality. Obfuscation makes it difficult for signature-based detection to identify malicious PowerShell scripts, as the underlying patterns are hidden beneath layers of encoding and restructuring.
String manipulation represents a fundamental obfuscation technique used in PowerSploit to avoid detection. Critical function names, commands, and parameters can be encoded, split, or reconstructed at runtime to avoid static analysis. These techniques are particularly effective against antivirus solutions that rely on pattern matching or simple keyword detection, as the malicious indicators are not present in a recognizable form until the script is executed.
Advanced encoding methods in PowerSploit can transform the entire script structure while preserving its functionality. These techniques might include Base64 encoding with custom keys, XOR operations, or even custom encryption schemes. By requiring the script to decode itself during execution, PowerSploit can evade static analysis while still performing its intended operations. This approach challenges security solutions to implement more sophisticated analysis capabilities that can decode or analyze obfuscated content.
Memory-Based Execution Techniques
Reflective loading is a particularly powerful technique employed by PowerSploit, enabling the execution of DLLs directly from memory without writing them to disk. This method bypasses many security controls that monitor file creation or execution, as the malicious code never exists as a standalone file. Reflective loading challenges antivirus solutions to implement memory scanning capabilities that can identify suspicious code patterns or structures during runtime.
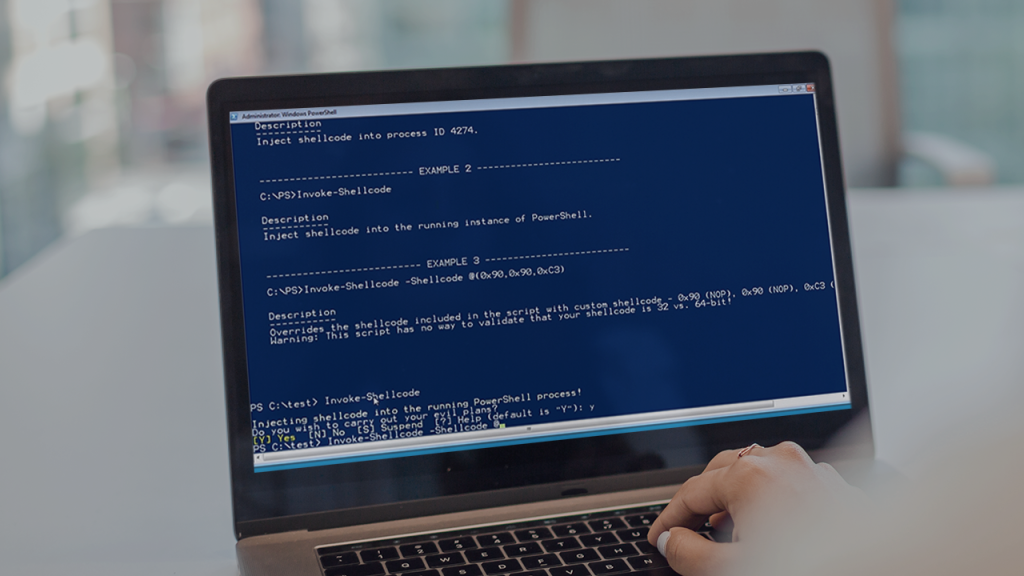
PowerSploit’s shellcode injection capabilities allow the toolkit to execute arbitrary code within the context of legitimate processes. This technique can bypass application whitelisting and process-based security controls by hiding malicious activities within trusted applications. The ability to inject code into running processes makes detection significantly more challenging, as the malicious operations appear to originate from legitimate system activities rather than unauthorized applications.
AMSI Bypassing Techniques
The Antimalware Scan Interface (AMSI) represents a significant challenge for PowerShell-based tools like PowerSploit, as it provides runtime script inspection capabilities. In response, PowerSploit has incorporated various techniques to bypass or disable AMSI protections. These methods range from simple configuration changes to more sophisticated approaches that manipulate memory or exploit implementation vulnerabilities in the AMSI framework.
Memory manipulation techniques can disable AMSI by modifying the function pointers or return values in memory during script execution. These approaches require elevated privileges but can effectively neutralize AMSI protections, allowing PowerSploit modules to execute without inspection. Memory-based bypasses are particularly challenging to detect, as they don’t involve suspicious file activities or obvious configuration changes.
PowerSploit also includes techniques that exploit legitimate AMSI functionality to avoid detection. These methods might involve fragmenting malicious code across multiple script executions or using approved PowerShell cmdlets in unintended ways. By working within the boundaries of legitimate functionality while achieving malicious objectives, these techniques challenge security solutions to implement more contextual and behavioral detection capabilities rather than relying solely on script content analysis.
Real-World Effectiveness Against Antivirus Solutions
Organizations that rely solely on traditional antivirus solutions without additional security layers are particularly vulnerable to PowerSploit-based attacks. These basic security products often lack the sophisticated behavioral analysis and memory scanning capabilities required to detect advanced PowerShell threats. In such environments, PowerSploit can often operate undetected, especially when combined with appropriate evasion techniques and careful operational security practices.
The effectiveness of PowerSploit against antivirus solutions also depends heavily on the specific modules and techniques employed. Some PowerSploit capabilities are inherently more detectable than others, with memory-based operations and code injection techniques typically triggering more alerts than information gathering or persistence mechanisms. Understanding these detection patterns allows security professionals to use PowerSploit effectively for testing while minimizing the risk of disruption to production environments.
Testing Against Traditional Antivirus Solutions
Traditional antivirus solutions often struggle to detect PowerSploit activities, particularly when the toolkit is used with appropriate evasion techniques. These security products typically focus on file-based scanning and signature-based detection, which can be bypassed through PowerSploit’s obfuscation and memory-based execution capabilities. In test environments, PowerSploit has demonstrated the ability to evade detection by numerous traditional antivirus products, especially when the modules are customized or modified.
PowerSploit’s effectiveness against traditional antivirus solutions has led many organizations to adopt more comprehensive endpoint protection platforms. These advanced solutions incorporate multiple detection layers, including behavioral analysis, memory scanning, and PowerShell-specific monitoring capabilities. The transition from traditional antivirus to these more sophisticated security products represents a direct response to the challenges posed by tools like PowerSploit and similar PowerShell-based attack frameworks.
Performance Against Advanced Endpoint Protection
Behavioral analysis capabilities in advanced endpoint protection can detect suspicious PowerShell activities even when the underlying code is obfuscated or modified. These solutions monitor for patterns indicative of malicious intent, such as unusual API calls, memory manipulation techniques, or privilege escalation attempts. PowerSploit operations that deviate significantly from normal administrative PowerShell usage are more likely to trigger alerts from these behavioral detection systems.
Machine learning models employed by advanced endpoint protection solutions can identify subtle patterns indicative of PowerSploit usage, even when specific signatures are not present. These models are trained on vast datasets of both legitimate and malicious PowerShell activities, allowing them to recognize suspicious behaviors that might escape simpler detection mechanisms. The effectiveness of these machine learning approaches against PowerSploit depends on the quality and diversity of the training data, as well as the ongoing model updates to address new evasion techniques.
Industry Case Studies and Observations
Financial services organizations, which typically maintain robust security controls, have still demonstrated vulnerabilities to PowerSploit-based attacks during security assessments. These cases often involve sophisticated evasion techniques and careful operational security practices to avoid detection. The success of PowerSploit even in highly regulated environments with mature security programs underscores the challenges faced by organizations in defending against PowerShell-based threats.
Healthcare and government sectors have also been targeted by PowerShell-based attacks similar to those facilitated by PowerSploit. Security assessments in these sectors frequently reveal that basic security controls are insufficient to detect or prevent PowerSploit activities, particularly when combined with social engineering or other attack vectors. These observations have led to increased focus on PowerShell security across industries, with organizations implementing specialized monitoring and protection solutions specifically designed to address these threats.
Detection and Mitigation Strategies
Organizations seeking to protect against PowerSploit and similar PowerShell-based threats must implement comprehensive security strategies that address the unique challenges posed by these attack tools. Effective protection requires multiple layers of security controls, from prevention to detection and response, each designed to address specific aspects of the PowerShell threat landscape. A holistic approach that combines technical controls with policies and user education provides the most robust defense against PowerSploit-based attacks.
The mitigation of PowerSploit threats requires both technical controls and operational changes to reduce the attack surface available to potential adversaries. These measures might include PowerShell execution policies, application whitelisting, credential protection, and network segmentation. By implementing defense-in-depth strategies that address multiple aspects of the attack chain, organizations can significantly reduce their vulnerability to PowerSploit-based attacks while maintaining necessary administrative capabilities.
PowerShell Security Best Practices
Implementing appropriate PowerShell execution policies represents a foundational step in securing against PowerSploit threats. Organizations should restrict PowerShell execution to only signed scripts or specific approved scenarios, reducing the attack surface available to adversaries. These execution policies should be enforced through Group Policy Objects (GPOs) to ensure consistent implementation across the enterprise environment, with exceptions carefully documented and approved through formal change management processes.
PowerShell logging and monitoring capabilities provide essential visibility into potentially malicious activities that might indicate PowerSploit usage. Organizations should enable comprehensive PowerShell logging, including module logging, script block logging, and transcription, to capture detailed information about PowerShell execution. This logging data should be forwarded to security information and event management (SIEM) systems for analysis and correlation with other security events.
Advanced Detection Technologies
Specialized PowerShell security solutions provide enhanced detection capabilities specifically designed to address threats like PowerSploit. These products offer deep visibility into PowerShell activities, behavioral analysis to identify suspicious patterns, and automated response capabilities to contain potential threats. Organizations should evaluate these specialized solutions as supplements to their existing security controls, particularly in environments where PowerShell is heavily used for administrative purposes.
Endpoint Detection and Response (EDR) solutions with PowerShell-specific monitoring capabilities can detect PowerSploit activities through behavioral analysis and anomaly detection. These platforms typically include machine learning models trained to recognize suspicious PowerShell usage patterns, memory scanning to detect code injection techniques, and integration with threat intelligence feeds to identify emerging attack methodologies. The comprehensive visibility provided by EDR solutions is particularly valuable for detecting sophisticated PowerSploit operations that might evade traditional security controls.
Incident Response and Recovery
Organizations should develop specific incident response procedures for suspected PowerSploit compromises, including isolation of affected systems, collection of forensic evidence, and analysis of PowerShell logs. These procedures should be regularly tested through tabletop exercises and simulations to ensure effectiveness during actual security incidents. The unique characteristics of PowerShell-based attacks require specialized response capabilities beyond general incident response processes.
Forensic analysis of potential PowerSploit incidents requires specialized tools and techniques to reconstruct PowerShell activities and identify the full scope of compromise. Organizations should maintain capabilities for analyzing PowerShell transcripts, module logs, and script block logs to understand attacker activities. This forensic information is essential for determining the extent of the breach, identifying affected systems, and preventing future compromises.
Future Developments and Trends
The ongoing evolution of both PowerSploit capabilities and antivirus detection technologies ensures that the relationship between these tools will continue to change over time. As security vendors develop more sophisticated detection mechanisms, PowerSploit and similar tools will adapt with new evasion techniques, creating a continuous cycle of innovation and countermeasures. Understanding these trends helps organizations prepare for future threats and implement security controls that will remain effective against evolving attack methodologies.
The integration of artificial intelligence and machine learning into both offensive and defensive security tools represents a significant trend that will shape the future of PowerSploit and antivirus technologies. These technologies enable more sophisticated behavioral analysis, anomaly detection, and automated response capabilities on the defensive side, while also providing new opportunities for evasion and stealth on the offensive side. This AI-driven arms race will likely accelerate the pace of innovation in both PowerSploit capabilities and detection technologies.
Emerging Evasion Techniques
Future versions of PowerSploit will likely incorporate more sophisticated evasion techniques leveraging artificial intelligence and machine learning. These advanced approaches might dynamically adapt to specific security environments, automatically selecting the most effective evasion methods based on the detected security controls. This intelligent adaptation would make PowerSploit significantly more challenging to detect, as the evasion techniques would vary between targets and even between multiple executions against the same target.
Living off the land techniques, which use legitimate system tools and features to achieve malicious objectives, will likely become more prevalent in future PowerSploit developments. These approaches minimize the attack surface by avoiding the introduction of external tools or files that might trigger security alerts. The expansion of living off the land techniques in PowerSploit will challenge organizations to implement more sophisticated behavioral analysis and anomaly detection capabilities that can identify malicious use of legitimate administrative tools.
Advancements in Detection Technologies
Future antivirus and endpoint protection solutions will likely incorporate more advanced artificial intelligence and machine learning models specifically trained to detect PowerSploit and similar PowerShell-based threats. These models will analyze vast datasets of both legitimate and malicious PowerShell activities, identifying subtle patterns and correlations that escape current detection approaches. The continuous learning capabilities of these AI systems will enable them to adapt to new PowerSploit techniques without requiring explicit signature updates or rule modifications.
Behavioral analysis technologies will become increasingly sophisticated, moving beyond simple pattern matching to understand the context and intent behind PowerShell activities. These advanced behavioral systems will develop more nuanced models of legitimate administrative PowerShell usage, allowing them to identify deviations that might indicate PowerSploit operations while minimizing false positives. The contextual understanding provided by these systems will significantly improve detection accuracy while reducing the operational impact on legitimate administrative activities.
Regulatory and Compliance Implications
The increasing regulatory focus on cybersecurity will likely drive new requirements specifically addressing PowerShell-based threats like those posed by PowerSploit. Compliance frameworks may mandate specific controls for PowerShell monitoring, execution restrictions, and logging requirements to ensure organizations can detect and respond to these sophisticated attack vectors. These regulatory requirements will create additional incentives for organizations to implement comprehensive PowerShell security strategies beyond general cybersecurity controls.
Industry-specific compliance requirements, particularly in highly regulated sectors like finance and healthcare, will likely include more detailed provisions for PowerShell security and protection against tools like PowerSploit. These sector-specific requirements may mandate specialized security controls, regular security assessments, and detailed reporting of PowerShell-related security incidents. The evolving compliance landscape will create both challenges and opportunities for organizations seeking to balance security requirements with operational needs.
PowerSploit’s ability to bypass antivirus varies significantly depending on the security solutions deployed and techniques employed. Traditional antivirus often fails to detect PowerSploit activities, while advanced endpoint protection presents greater challenges through behavioral analysis and memory scanning. Organizations must implement comprehensive PowerShell security strategies including execution policies, logging, and specialized monitoring solutions. The ongoing evolution of both PowerSploit capabilities and detection technologies ensures this remains a dynamic area requiring continuous attention from security professionals.