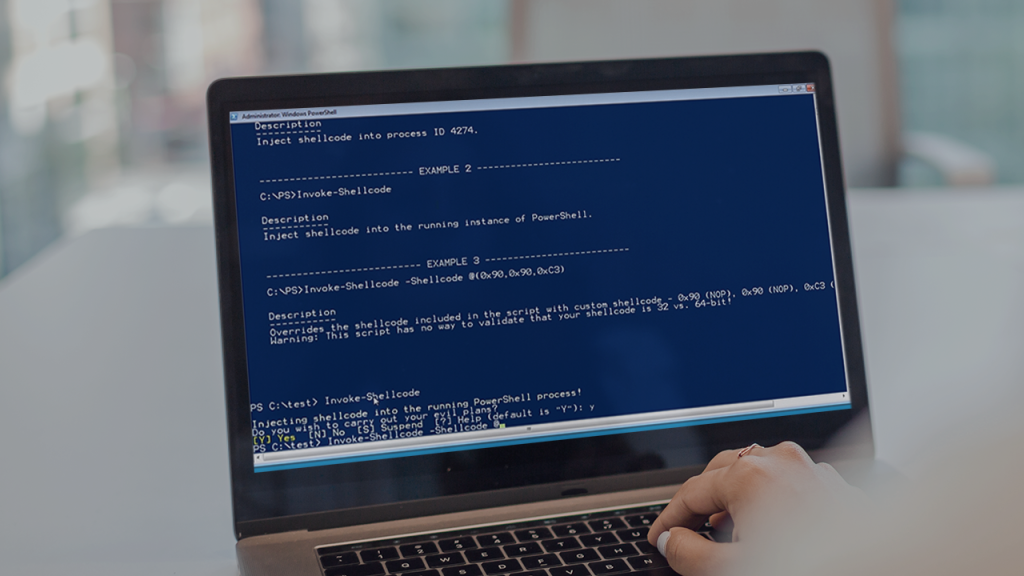
PowerSploit stands as a powerful collection of Microsoft PowerShell modules designed for penetration testing, security assessments, and post-exploitation activities. Developed with cybersecurity professionals in mind, this open-source project has gained significant traction within the security community since its inception. The toolset provides capabilities ranging from code execution to credential harvesting, making it an invaluable resource for those tasked with identifying and addressing security vulnerabilities in Windows environments.
The versatility of PowerSploit has contributed to its widespread adoption across various sectors of the cybersecurity landscape. Security researchers, ethical hackers, and red team professionals leverage its capabilities to simulate real-world attack scenarios, helping organizations strengthen their defensive postures. The tool’s integration with PowerShell, a native Windows scripting language, allows for seamless operation within target environments without raising immediate suspicion from security systems that might flag more obvious penetration testing tools.
As organizations increasingly prioritize cybersecurity measures, understanding who utilizes PowerSploit and for what purposes becomes essential. This article explores the primary users of this powerful toolkit, examining their motivations, methodologies, and the contexts in which PowerSploit proves most valuable. By understanding these user profiles, security professionals can better anticipate potential threats and develop more robust defensive strategies against malicious actors who might also exploit these same capabilities.
Penetration Testers and Ethical Hackers
Corporate Security Assessments
Penetration testers regularly employ PowerSploit during authorized security assessments of corporate networks and systems. These cybersecurity professionals simulate real-world attacks to identify vulnerabilities before malicious actors can exploit them. PowerSploit’s modules enable testers to evaluate the effectiveness of existing security controls, discover potential entry points, and assess the overall security posture of an organization’s IT infrastructure. The tool’s ability to operate within legitimate PowerShell processes makes it particularly valuable for testing security monitoring and detection capabilities.
Third-Party Security Services
Security consulting firms and managed security service providers frequently integrate PowerSploit into their testing methodologies. These organizations offer specialized penetration testing services to clients across various industries, utilizing the toolkit to conduct comprehensive security evaluations. PowerSploit’s versatility allows these service providers to customize their testing approaches based on client requirements, industry regulations, and specific threat environments. The tool’s open-source nature also means it can be modified to address unique testing scenarios or compliance requirements.
Freelance Security Researchers
Independent security researchers and freelance penetration testers often rely on PowerSploit due to its accessibility and comprehensive feature set. These professionals appreciate the tool’s cost-effectiveness (being free and open-source) and its active community support. Freelance testers typically work with diverse clients across different sectors, requiring flexible tools that can adapt to various environments. PowerSploit’s modular architecture allows these researchers to select only the components relevant to specific engagements, creating streamlined testing approaches tailored to individual client needs.
Red Team Professionals
Enterprise Security Testing
Red team specialists within large organizations utilize PowerSploit to conduct sophisticated attack simulations against their own employers’ systems. These professionals operate under the principle of “thinking like attackers” to identify weaknesses that might be exploited by actual threat actors. PowerSploit enables red teamers to emulate advanced persistent threats (APTs) and other sophisticated attack techniques, providing realistic assessments of an organization’s detection and response capabilities. The tool’s stealth capabilities allow red teamers to operate undetected for extended periods, testing the effectiveness of security monitoring systems.
- Red team exercises using PowerSploit often focus on lateral movement techniques, testing how easily attackers can navigate through a network after initial compromise
- The toolkit’s persistence mechanisms help evaluate whether security teams can detect and remove unauthorized access methods
- PowerSploit’s credential harvesting capabilities test the effectiveness of password policies and access controls
- Data exfiltration modules assess whether sensitive information can be identified and transferred without detection
- Privilege escalation features determine if attackers can gain higher-level access to critical systems
Advanced Threat Simulation
Security teams dedicated to threat intelligence and defense often employ PowerSploit to replicate techniques observed in actual cyberattacks. By studying threat actor reports and malware analysis, these professionals can recreate attack chains using PowerSploit’s modules. This approach helps organizations understand their specific risk profile based on industry, size, and other factors. The ability to customize and combine various PowerSploit functions allows for the recreation of complex, multi-stage attacks that closely mirror real-world threats.
Purple Team Collaboration
Purple teams, which combine offensive (red) and defensive (blue) security personnel, leverage PowerSploit to enhance collaboration between these traditionally separate functions. These teams use the toolkit to execute controlled attacks while simultaneously monitoring defensive responses, creating immediate feedback loops for security improvement. PowerSploit’s transparent operation allows blue team members to understand exactly what indicators of compromise to watch for in real-world scenarios. This collaborative approach helps organizations develop more effective detection rules and response procedures based on actual attack techniques rather than theoretical threats.
Malicious Actors and Cybercriminals
Ransomware Operators
Unfortunately, the same capabilities that make PowerSploit valuable for security professionals also attract malicious actors seeking to compromise systems. Ransomware operators frequently incorporate PowerSploit techniques into their attack chains, particularly for lateral movement and privilege escalation within compromised networks. The tool’s ability to execute code remotely and harvest credentials makes it ideal for attackers seeking to maximize their reach across an organization’s infrastructure before deploying encryption payloads. These criminals often modify PowerSploit modules to evade detection by security solutions specifically designed to identify known PowerSploit usage patterns.
State-Sponsored Attackers
Advanced persistent threat groups associated with nation-states have been observed utilizing PowerSploit-derived techniques in their operations. These sophisticated threat actors value the tool’s ability to operate within legitimate system processes, making detection more challenging. State-sponsored attackers often combine PowerSploit capabilities with custom-developed tools to create unique attack signatures that don’t match known patterns. The toolkit’s modular nature allows these groups to select only the functions needed for specific operations, creating streamlined attack tools tailored to particular targets or environments.
Financial Fraudsters
Cybercriminals focused on financial gain leverage PowerSploit to facilitate various forms of fraud and theft. These attackers use the toolkit to harvest credentials, move laterally through networks to identify valuable targets, and establish persistence for ongoing access. PowerSploit’s ability to manipulate authentication processes makes it particularly valuable for attackers seeking to impersonate legitimate users or access sensitive financial systems. The tool’s data exfiltration capabilities also enable these criminals to identify and extract valuable information for direct financial gain or for sale on underground markets.
Cybersecurity Educators and Students
University Programs
Cybersecurity education programs at universities and colleges increasingly incorporate PowerSploit into their curricula. Students learning penetration testing, ethical hacking, and defensive security techniques benefit from hands-on experience with industry-standard tools. PowerSploit’s open-source nature makes it accessible to educational institutions with limited budgets, while its comprehensive feature set provides exposure to multiple attack techniques within a single toolkit. Professors can design practical exercises that demonstrate various aspects of cybersecurity, from initial reconnaissance to post-exploitation activities.
Professional Training Centers
Commercial cybersecurity training organizations frequently include PowerSploit in their certification preparation courses and specialized workshops. These training centers focus on practical skills development, using the toolkit to teach real-world penetration testing methodologies. Students preparing for certifications like OSCP, CEPT, or other offensive security credentials benefit from PowerSploit’s alignment with common examination objectives. Training providers value the tool’s ability to demonstrate complex concepts through practical application rather than theoretical instruction alone.
Capture the Flag Competitions
PowerSploit features prominently in cybersecurity competitions and capture the flag (CTF) events. These challenges, designed to test participants’ security skills in competitive environments, often include scenarios where PowerSploit provides an advantage. Contest organizers create challenges specifically around PowerSploit capabilities, testing participants’ familiarity with the toolkit’s modules and techniques. These competitive environments help develop practical skills while fostering innovation in attack and defense methodologies among the next generation of cybersecurity professionals.
Security Researchers and Vulnerability Analysts
Zero-Day Discovery
Security researchers dedicated to discovering new vulnerabilities utilize PowerSploit to test potential security weaknesses in Windows environments. The toolkit’s ability to interact with system components at low levels makes it valuable for probing for undiscovered flaws. Researchers often combine PowerSploit with fuzzing techniques and custom scripts to identify previously unknown vulnerabilities that could be exploited by malicious actors. This proactive approach to vulnerability discovery helps software vendors and organizations patch issues before they can be weaponized by attackers.
Exploit Development
Once vulnerabilities are identified, security researchers leverage PowerSploit to develop proof-of-concept exploits that demonstrate the security issue. These exploits help validate the severity of vulnerabilities and provide vendors with clear examples of potential attacks. PowerSploit’s modular architecture allows researchers to create focused exploits targeting specific components while maintaining clean, reusable code. The toolkit’s integration with PowerShell also enables the creation of exploits that operate within legitimate system processes, closely mimicking how real attackers might exploit the same vulnerabilities.
Security Tool Evaluation
Professionals tasked with evaluating security products and solutions use PowerSploit to test the effectiveness of these tools against real-world attack techniques. By employing PowerSploit modules in controlled environments, researchers can assess whether security solutions adequately detect and prevent various attack vectors. This evaluation process helps organizations make informed decisions about security investments and provides vendors with valuable feedback for improving their products. PowerSploit’s comprehensive coverage of attack techniques makes it particularly valuable for thorough security product assessments.
System Administrators and IT Professionals
Security Auditing
System administrators increasingly incorporate PowerSploit techniques into their regular security auditing processes. By using the same tools employed by attackers, these professionals can identify potential vulnerabilities in their systems before they can be exploited. PowerSploit’s ability to scan for misconfigurations, weak permissions, and other security issues provides administrators with actionable insights for improving their security posture. This proactive approach to security helps organizations maintain stronger defenses against potential threats while ensuring compliance with security standards and regulations.
- Permission analysis modules help administrators identify overly permissive access controls that could be exploited by attackers
- Service configuration scanning reveals potentially vulnerable services running with excessive privileges
- Registry examination tools detect security-related settings that may have been modified or improperly configured
- Cryptography analysis capabilities assess the strength of encryption implementations across the system
- Network protocol testing evaluates the security of network services and potential attack vectors
Incident Response Preparation
IT professionals responsible for incident response utilize PowerSploit to prepare for potential security breaches. By understanding how attackers might use these tools against their systems, responders can develop more effective detection and mitigation strategies. PowerSploit’s capabilities help administrators understand potential attack paths that adversaries might follow, allowing for the development of more comprehensive incident response playbooks. This preparation enables faster, more effective responses when actual security incidents occur, minimizing potential damage and recovery time.
Security Awareness Training
System administrators and IT security professionals leverage PowerSploit demonstrations to enhance security awareness among non-technical staff. By showing how easily certain attacks can be executed using these tools, administrators can emphasize the importance of security best practices to employees at all levels. These practical demonstrations often prove more impactful than theoretical explanations of security risks, helping create a more security-conscious organizational culture. PowerSploit’s ability to demonstrate various attack techniques makes it valuable for creating engaging, educational security awareness sessions.
Conclusion
PowerSploit serves diverse user groups across the cybersecurity landscape, from ethical hackers strengthening defenses to malicious actors seeking to exploit vulnerabilities. Its accessibility, versatility, and integration with PowerShell make it a valuable tool for penetration testing, security research, education, and unfortunately, cybercrime. Understanding these varied users helps organizations develop more comprehensive security strategies addressing both legitimate security testing and potential threats. As PowerSploit continues to evolve, its user base will likely expand, further cementing its role in the cybersecurity toolkit ecosystem.