PowerSploit stands as one of the most powerful penetration testing frameworks in the cybersecurity landscape, offering security professionals a comprehensive toolkit for assessing Windows environments. Developed primarily for offensive security testing, this PowerShell-based collection has become an industry standard for ethical hackers and red teamers worldwide. Understanding its privilege requirements is essential for both security practitioners implementing tests and defenders building detection mechanisms.
The question of administrative privileges frequently arises when discussing PowerSploit implementation, as the answer significantly impacts testing methodologies and potential security outcomes. Many organizations struggle with determining the appropriate access levels needed for comprehensive security assessments while maintaining operational integrity. This nuanced aspect of PowerSploit functionality deserves thorough examination to ensure proper utilization without unnecessary system exposure.
Security professionals must recognize that PowerSploit privilege requirements vary considerably depending on the specific modules and intended operations. While some functions demand elevated permissions to access sensitive system components or modify critical configurations, others can operate effectively with standard user privileges. This flexibility makes PowerSploit particularly valuable across diverse testing scenarios where administrative access may not always be available or desirable.
Understanding PowerSploit and Its Core Functionality
What is PowerSploit?
PowerSploit represents a collection of PowerShell modules designed specifically for penetration testing and security assessments of Windows environments. Developed as an open-source project, it provides security professionals with tools for reconnaissance, privilege escalation, persistence, and exfiltration. The framework leverages PowerShell’s deep integration with Windows systems, allowing for sophisticated operations that might otherwise require multiple specialized tools.
The modular nature of PowerSploit enables security testers to select specific components relevant to their assessment objectives. Each module focuses on particular security testing aspects, from information gathering to exploitation techniques. This specialization allows for targeted testing approaches while maintaining a cohesive framework that integrates seamlessly with existing security workflows.
PowerSploit’s development has been community-driven, with contributions from security professionals worldwide. This collaborative approach ensures the framework remains current with evolving Windows security features and emerging attack techniques. The continuous updates reflect the dynamic nature of Windows security environments and the corresponding need for adaptable testing methodologies.
Primary Components of PowerSploit
The PowerSploit framework comprises several distinct modules, each serving specific penetration testing functions. These include CodeExecution for running arbitrary code, Persistence for maintaining access, Privesc for privilege escalation, Recon for information gathering, and Exfiltration for data extraction. Each module contains multiple functions designed to address particular security testing scenarios within Windows environments.
CodeExecution modules enable security testers to execute code in various contexts, helping identify potential vulnerabilities in application security controls. These components are particularly valuable for testing application whitelisting solutions and other security controls that might restrict code execution. The flexibility of these modules allows for testing across different permission levels and security contexts.
Persistence mechanisms within PowerSploit focus on maintaining access to compromised systems, simulating advanced persistent threats. These tools create backdoors and alternative access methods that attackers might employ after initial system compromise. Understanding these persistence techniques is crucial for organizations developing detection capabilities against sophisticated threats.
Evolution of PowerSploit in Cybersecurity
Since its initial release, PowerSploit has undergone significant evolution to address changing Windows security landscapes. The framework has adapted to new security features introduced in Windows versions, ensuring continued relevance for security testing. This evolution reflects the ongoing cat-and-mouse game between offensive security tools and defensive measures implemented by Microsoft and other security vendors.
The increasing adoption of PowerShell for legitimate administrative tasks has necessitated more sophisticated approaches to both offensive and defensive PowerShell usage. PowerSploit has evolved to incorporate techniques that bypass common security controls while maintaining functionality. This evolution demonstrates the framework’s adaptability to emerging security challenges and detection mechanisms.
Recent developments in PowerSploit have focused on operational security for penetration testers, incorporating features that reduce detection likelihood while maintaining effectiveness. These developments reflect the growing sophistication of enterprise security monitoring and the corresponding need for more subtle testing approaches that closely mimic real-world attack techniques.
Admin Privileges and PowerSploit: The Connection
Definition of Admin Privileges
Administrative privileges in Windows environments represent elevated permissions that allow users to perform system-wide changes and access protected resources. These privileges include the ability to install software, modify system configurations, access other user accounts, and alter security settings. Admin rights are typically reserved for IT personnel and are carefully controlled in enterprise environments due to their potential for system-wide impact.
The Windows privilege model implements various levels of administrative access, from standard users with limited permissions to domain administrators with extensive control over network resources. This hierarchical structure ensures appropriate access controls while enabling necessary administrative functions. Understanding these privilege levels is essential for determining PowerSploit’s operational capabilities in different contexts.
Administrative privileges are particularly significant in security contexts because they often represent the ultimate objective for attackers seeking system compromise. Once obtained, admin rights enable attackers to establish persistence, exfiltrate data, and move laterally across networks. This makes understanding admin privilege requirements crucial for both offensive security testing and defensive strategy development.
How PowerSploit Interacts with System Permissions
PowerSploit’s interaction with system permissions varies considerably depending on the specific module and intended operation. Some functions require administrative privileges to access sensitive system components or modify critical configurations. These elevated requirements typically apply to modules dealing with system-level changes, credential harvesting, or persistence mechanisms that need to modify system settings.
- Privilege escalation modules within PowerSploit specifically target administrative rights acquisition
- Information gathering functions often operate with standard user permissions
- Persistence mechanisms typically require elevated access to modify system configurations
- Code execution capabilities vary based on intended target and security context
- Exfiltration tools may function with different permission levels depending on target data location
The framework’s design acknowledges that penetration testers may not always have administrative access during initial phases of testing. Many PowerSploit modules are specifically designed to operate with standard user permissions, allowing for initial reconnaissance and information gathering before attempting privilege escalation. This tiered approach enables comprehensive testing regardless of initial permission levels.
PowerSploit’s permission requirements also reflect real-world attack scenarios where attackers often begin with limited access before escalating privileges. This design philosophy makes the framework particularly valuable for simulating realistic attack paths and identifying potential security gaps in privilege management systems.
Common Misconceptions About PowerSploit Requirements
A prevalent misconception about PowerSploit is that all modules require administrative privileges to function effectively. This misunderstanding often leads organizations to either underutilize the framework or unnecessarily restrict its usage. In reality, many PowerSploit modules are specifically designed to operate with standard user permissions, making them valuable for testing environments where admin access is limited or unavailable.
Another common misconception relates to the perceived necessity of admin rights for meaningful security testing with PowerSploit. While administrative privileges certainly expand testing capabilities, significant security insights can be gained even with limited permissions. Many critical vulnerabilities can be identified and assessed using standard user access, particularly those related to information disclosure, configuration weaknesses, or application-level security issues.
Some security professionals mistakenly believe that PowerSploit’s effectiveness is directly proportional to the level of system access available. While higher privileges certainly enable more comprehensive testing, the framework’s modular design allows for targeted testing at various permission levels. This flexibility ensures valuable security assessments regardless of initial access limitations.
PowerSploit Modules Requiring Admin Privileges
Privilege Escalation Modules
PowerSploit’s privilege escalation modules specifically target the acquisition of administrative rights from limited user accounts. These modules exploit various Windows vulnerabilities or misconfigurations that allow privilege elevation. The PowerUp module, for instance, examines Windows systems for common privilege escalation opportunities, including service misconfigurations, weak permissions, and vulnerable registry settings.
The Get-System function within PowerSploit attempts to gain SYSTEM-level privileges by abusing Windows token impersonation or other techniques. This capability is particularly valuable for penetration testers seeking to demonstrate the potential impact of initial compromise. These modules typically require some level of initial access but don’t necessarily need admin privileges to begin their operations.
Other privilege escalation tools in PowerSploit target specific vulnerabilities or Windows features that can be exploited for elevated access. These modules are regularly updated to incorporate newly discovered privilege escalation techniques, ensuring the framework remains effective against current Windows versions and security configurations. The continuous evolution of these modules reflects the ongoing discovery of privilege escalation vectors in Windows environments.
Persistence Mechanisms
PowerSploit’s persistence modules focus on maintaining access to compromised systems, typically requiring administrative privileges to modify system configurations or create backdoors. These modules simulate the techniques used by advanced persistent threats to maintain presence within target networks. The persistence capabilities include registry modifications, scheduled tasks, WMI event subscriptions, and service creation.
The registry-based persistence mechanisms modify Windows registry settings to execute malicious code during system startup or user login. These techniques require administrative access to modify protected registry keys but are highly effective for maintaining long-term access. PowerSploit provides various registry persistence options, each with different stealth characteristics and detection difficulty levels.
WMI-based persistence represents a more sophisticated approach that leverages Windows Management Instrumentation for maintaining access. These techniques create event subscriptions that trigger malicious code execution based on specific system events. While highly effective, WMI persistence requires administrative privileges and can be more difficult to detect than traditional persistence mechanisms.
Credential Harvesting Tools
PowerSploit’s credential harvesting modules are designed to extract sensitive authentication information from compromised systems, typically requiring administrative privileges to access protected credential stores. The Invoke-Mimikatz module, for instance, leverages the well-known Mimikatz tool to extract passwords, hashes, and Kerberos tickets from system memory.
These credential harvesting tools can extract various types of authentication data, including clear-text passwords, NTLM hashes, and Kerberos tickets. The extracted credentials can be used for lateral movement within the target network or for escalating privileges to more sensitive systems. The effectiveness of these tools typically depends on the level of access available on the compromised system.
PowerSploit also includes modules for extracting credentials from web browsers, email clients, and other applications that store authentication information. These tools often require administrative privileges to access protected application data stores but can provide valuable credentials for further network compromise. The comprehensive nature of these tools makes PowerSploit particularly valuable for credential-focused penetration testing.
PowerSploit Modules Without Admin Requirements
Information Gathering Capabilities
PowerSploit’s information gathering modules are specifically designed to operate with standard user permissions, making them valuable for initial reconnaissance phases of penetration testing. These modules can collect extensive system and network information without requiring elevated privileges. The Get-ComputerDetails function, for instance, gathers comprehensive system information including installed applications, network configuration, and security settings.
The network discovery capabilities in PowerSploit can identify systems, services, and potential vulnerabilities without administrative access. These tools leverage standard Windows networking functions to map network topology and identify potential attack vectors. The information gathered can guide subsequent testing phases and help identify the most promising privilege escalation opportunities.
PowerSploit’s reconnaissance modules also include tools for file searching, user enumeration, and system configuration analysis. These capabilities can identify sensitive files, misconfigured permissions, or other security weaknesses that might be exploitable without administrative access. The comprehensive nature of these information gathering tools makes PowerSploit valuable even when operating with limited permissions.
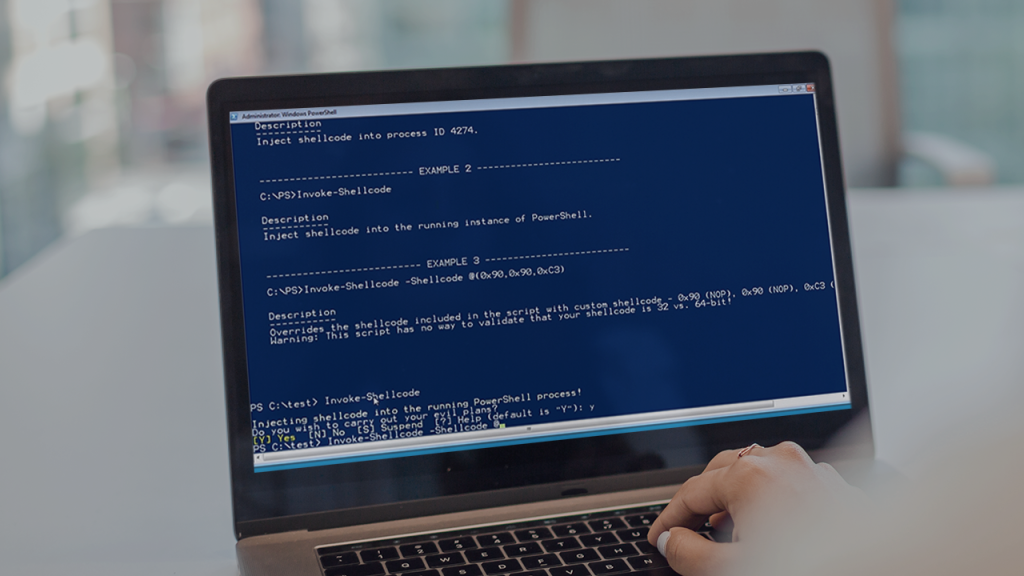
Code Execution Options
PowerSploit provides various code execution modules that can function with standard user permissions, allowing penetration testers to run arbitrary code in different contexts. The Invoke-Shellcode module, for instance, can execute shellcode in memory without requiring administrative privileges. These capabilities are particularly valuable for testing application security controls and identifying potential code execution vulnerabilities.
The framework’s code execution options include techniques for bypassing application whitelisting and other security controls that might restrict code execution. These methods often leverage legitimate Windows binaries or scripting techniques to execute unauthorized code. While some advanced techniques may require administrative privileges, many effective code execution methods work with standard user permissions.
PowerSploit’s code execution capabilities also include tools for running PowerShell commands in alternative contexts or with different tokens. These techniques can be particularly valuable for testing security controls that monitor or restrict PowerShell usage. The diversity of code execution options ensures penetration testers can effectively test application security regardless of available permission levels.
Network Discovery Tools
PowerSploit’s network discovery modules can identify and analyze network resources without requiring administrative privileges on the local system. These tools leverage standard Windows networking functions to map network topology, identify active systems, and enumerate available services. The information gathered can guide subsequent testing phases and help identify potential targets for privilege escalation.
The port scanning capabilities in PowerSploit can identify open ports and running services on network systems, potentially revealing vulnerable services or misconfigured security controls. These scans can be performed with standard user permissions, making them valuable for initial network reconnaissance. The detailed service information gathered can help identify potential attack vectors for further exploitation.
PowerSploit also includes modules for SNMP enumeration, DNS analysis, and other network protocol inspection. These tools can gather valuable network information without requiring elevated privileges, providing penetration testers with comprehensive network visibility. The extensive network discovery capabilities make PowerSploit particularly valuable for mapping network environments and identifying potential security weaknesses.
Implementing PowerSploit in Different Privilege Contexts
Enterprise Environment Considerations
Implementing PowerSploit in enterprise environments requires careful consideration of existing security controls and operational constraints. Many organizations implement application whitelisting, PowerShell logging, and other security measures that may impact PowerSploit’s effectiveness. Understanding these constraints is essential for planning comprehensive security assessments that provide meaningful results while minimizing operational disruption.
The modular nature of PowerSploit allows for tailored implementation based on specific enterprise environments and testing objectives. Security professionals can select appropriate modules based on available permissions and security control configurations. This flexibility ensures valuable security insights regardless of the enterprise environment’s security posture or access limitations.
Enterprise testing with PowerSploit should also consider potential impacts on production systems and user productivity. While many modules can operate safely with standard permissions, some administrative functions might cause system changes or service disruptions. Proper planning and communication are essential for balancing security assessment thoroughness with operational requirements.
Penetration Testing Scenarios
PowerSploit is particularly valuable in penetration testing scenarios where security professionals simulate realistic attack paths against target systems. The framework’s tiered approach to privilege requirements mirrors real-world attack scenarios where attackers typically begin with limited access before escalating privileges. This makes PowerSploit ideal for demonstrating potential security impacts and prioritizing remediation efforts.
In black-box penetration testing scenarios where testers have no prior knowledge of the target environment, PowerSploit’s information gathering modules can provide valuable initial insights. These modules operate effectively with limited permissions, allowing testers to identify potential attack vectors before attempting privilege escalation. The comprehensive reconnaissance capabilities guide subsequent testing phases for maximum efficiency.
White-box penetration testing scenarios benefit from PowerSploit’s ability to test specific security controls or configurations with known vulnerabilities. The framework’s modular approach allows testers to focus on particular security aspects relevant to the testing scope. This targeted approach ensures comprehensive testing of critical security controls while optimizing testing time and resources.
Red Team Operations Best Practices
Red team operations benefit significantly from PowerSploit’s comprehensive capabilities and flexible privilege requirements. The framework’s modular design allows red teamers to select appropriate tools based on specific engagement objectives and available access levels. This flexibility ensures realistic attack simulations while minimizing potential disruption to production environments.
PowerSploit’s stealth capabilities make it particularly valuable for red team operations where detection avoidance is crucial. Many modules incorporate techniques to minimize logging and other detection indicators, simulating sophisticated attacker behavior. These stealth features are particularly important when testing an organization’s detection and response capabilities.
Red team operations should carefully document PowerSploit usage and results to provide valuable security insights for blue team improvements. The detailed information gathered during operations can help identify security gaps, prioritize remediation efforts, and improve overall security posture. This documentation also ensures compliance with engagement requirements and facilitates knowledge transfer to security teams.
Alternatives to PowerSploit for Non-Admin Contexts
PowerShell Empire
PowerShell Empire represents a comprehensive post-exploitation framework that offers alternatives to PowerSploit in contexts where administrative privileges are unavailable. This framework provides similar capabilities to PowerSploit but with different implementation approaches that may be more suitable for certain testing scenarios. Empire’s modular architecture allows for customized operations based on specific testing requirements.
The agent-based approach of PowerShell Empire differs from PowerSploit’s module-based structure, providing persistent communication channels for extended operations. This design makes Empire particularly valuable for longer-term assessments or scenarios requiring sustained access. The framework’s diverse communication options help bypass network security controls that might restrict other tools.
PowerShell Empire also incorporates operational security features that make it suitable for testing advanced detection capabilities. These features include traffic encryption, communication diversification, and other techniques to avoid common security monitoring. The focus on stealth makes Empire particularly valuable for testing sophisticated security environments.
Covenant Framework
Covenant represents a modern alternative to PowerSploit that offers a web-based interface and advanced operational capabilities. This .NET command and control framework provides similar functionality to PowerSploit but with different implementation approaches that may be more suitable for certain testing scenarios. Covenant’s graphical interface makes it particularly accessible for security professionals with varying technical expertise.
The listener-based architecture of Covenant allows for diverse communication methods that can bypass network security controls. This flexibility makes the framework valuable for testing environments with restrictive network policies or advanced security monitoring. Covenant’s modular design also enables customized operations based on specific testing requirements.
Covenant incorporates operational security features designed to avoid common detection mechanisms while maintaining functionality. These features include traffic analysis resistance, process injection techniques, and other advanced capabilities. The framework’s modern implementation makes it particularly effective against current security solutions and monitoring approaches.
Custom PowerShell Scripts
Custom PowerShell scripts provide flexible alternatives to PowerSploit when specific testing requirements aren’t addressed by existing modules. These scripts can be tailored to particular environments or security control configurations, offering targeted testing capabilities. The extensibility of PowerShell makes it possible to create custom solutions for virtually any security testing scenario.
Developing custom PowerShell scripts allows security professionals to incorporate organization-specific knowledge into testing methodologies. These scripts can address unique system configurations, custom applications, or specialized security controls that might not be adequately tested by generic tools. The tailored approach ensures comprehensive testing of the specific environment rather than general security aspects.
Custom PowerShell scripts can also be designed to operate within specific permission constraints, ensuring functionality regardless of available access levels. This flexibility makes custom scripts particularly valuable for environments with restrictive security policies or limited administrative access. The ability to create precisely targeted testing tools ensures comprehensive security assessments regardless of environmental constraints.
Conclusion
PowerSploit’s privilege requirements vary significantly across its modules, with some functions needing administrative access while others operate effectively with standard user permissions. This flexibility makes the framework valuable across diverse testing scenarios and environments. Security professionals should carefully select appropriate modules based on available permissions and testing objectives to ensure comprehensive assessments. Understanding these privilege requirements enables more effective security testing and better preparation against real-world attack scenarios. The framework’s modular design ensures valuable security insights regardless of initial access limitations.